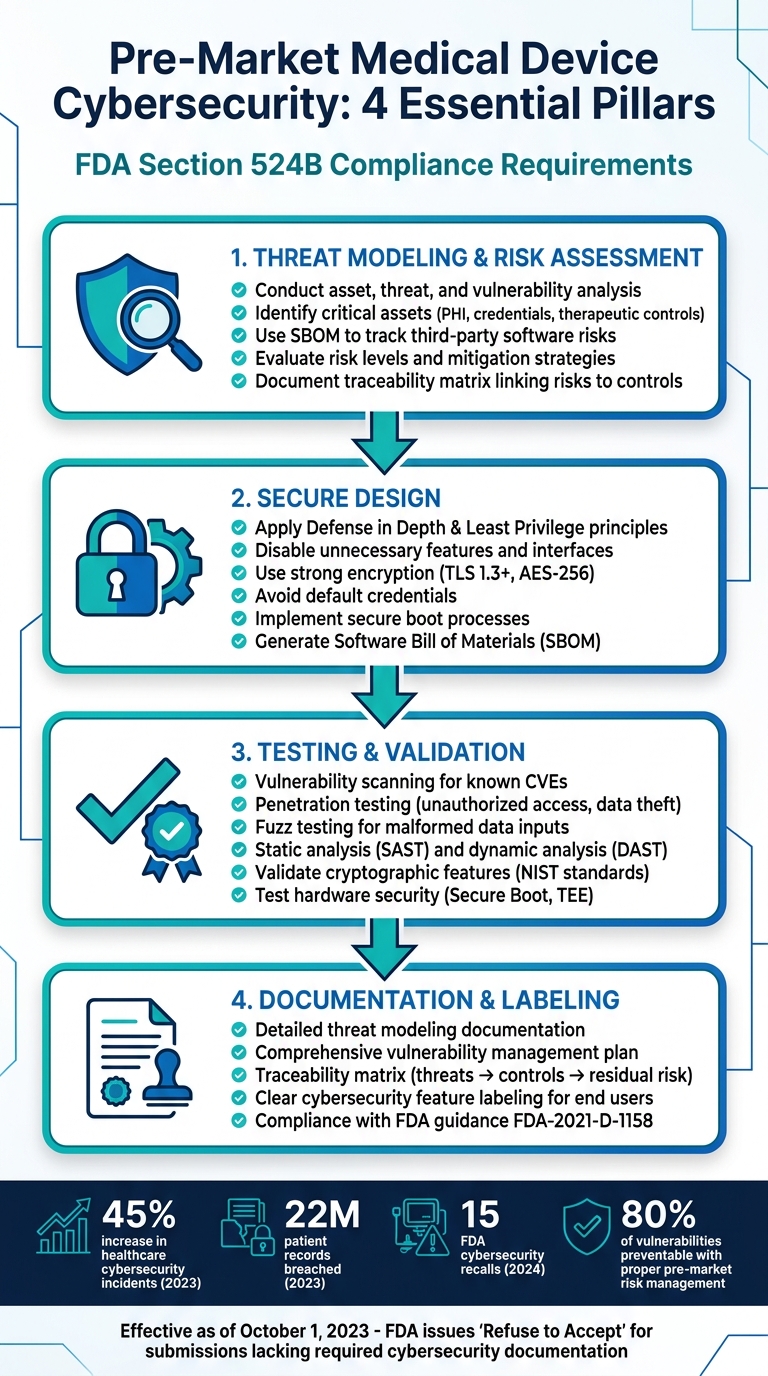
Medical devices connected to networks, like insulin pumps or cardiac monitors, face medical device security risks that could compromise patient safety. To tackle this, the FDA now requires manufacturers to meet specific pre-market cybersecurity standards under Section 524B of the FD&C Act. These rules ensure devices are secure before entering the market. Here's a quick breakdown of what manufacturers need to do:
- Threat Modeling & Risk Assessment: Identify device vulnerabilities early, assess risks, and plan mitigations. Use tools like SBOMs (Software Bill of Materials) to track third-party software risks.
- Secure Design: Follow principles like "Defense in Depth" and "Least Privilege." Disable unnecessary features, use strong encryption, and avoid default credentials.
- Testing: Conduct vulnerability scans, penetration testing, and cryptographic validation to confirm devices can withstand attacks.
- Documentation: Maintain detailed records like traceability matrices, vulnerability management plans, and cybersecurity feature labeling for FDA submissions.
Tools like Censinet RiskOps™ can help streamline these processes by automating documentation and risk assessments. Meeting these requirements not only protects patients but also ensures faster regulatory approval.
FDA Pre-Market Medical Device Cybersecurity Compliance Checklist
Webinar: Master Medical Device Cybersecurity: Avoid FDA Delays

sbb-itb-535baee
Threat Modeling and Risk Assessment Checklist
Threat modeling and risk assessment are crucial steps in achieving pre-market cybersecurity compliance. These methods help manufacturers pinpoint potential vulnerabilities in connected medical devices before they hit the market. The FDA mandates that this analysis begins during the requirements phase, not as a last-minute task after development. This proactive mindset aligns with the principle of secure-by-design, ensuring threats are addressed throughout the entire development process.
Conduct Asset, Threat, and Vulnerability Analysis
Start by identifying all critical assets that need protection, such as PHI (Protected Health Information), therapeutic control parameters, authentication credentials, and core functionalities [3]. Then, map out attack surfaces and define system boundaries through threat modeling. This step involves documenting potential ways an attacker might target the device, like exploiting network connections to healthcare systems or cloud services.
To manage vulnerabilities effectively, use an SBOM (Software Bill of Materials) to track third-party components [3]. Since medical devices often remain in use for 10 to 15 years or more, your risk management approach must adapt to evolving threats throughout the device's lifecycle [3].
Once assets and threats are clearly outlined, dive into assessing risks and planning mitigation strategies.
Evaluate Risk Levels and Mitigation Strategies
For each identified threat, evaluate both its likelihood and potential severity. Use secure design principles like Defense in Depth and Least Privilege to create layered protections against risks, considering not only digital threats but also traditional physical hazards [3].
Define specific criteria for residual risk to determine when a device is secure enough for market release. The FDA stresses that the level of cybersecurity design and documentation should match the device's risk level [2]. As of October 1, 2023, the FDA has started issuing "Refuse to Accept" decisions for premarket submissions that lack the required cybersecurity documentation [2].
Once risks and mitigation strategies are established, organize and document this information systematically.
Document a Traceability Matrix
A traceability matrix links each identified cybersecurity risk to its corresponding control and mitigation. This ensures no security gaps exist between your threat modeling and risk assessment [5]. According to the FDA's 2025 premarket cybersecurity guidance, threat modeling must "identify medical device system risks and mitigations as well as inform the pre- and post-mitigation risks considered as part of the cybersecurity risk assessment" [5].
| Traceability Element | Description |
|---|---|
| Threat Scenarios | Attack scenarios identified during threat modeling |
| Risk Entries | Related entries in the cybersecurity risk assessment for each scenario |
| Risk Controls | Security measures implemented to mitigate identified threats |
| Residual Risk | Remaining risk level after applying controls |
Keep the traceability matrix updated whenever there are changes to threat models or risk assessments during development [5]. This dynamic document provides a clear map of how every security control addresses a specific risk. It also serves as evidence for regulators, demonstrating the device's security posture across its lifecycle.
Secure Product Development Framework Checklist
Incorporating cybersecurity into every phase of product development is no longer optional - it's a requirement. The FDA mandates that manufacturers prioritize security from the very beginning, ensuring that every design decision considers potential threats. This framework outlines how to embed security into your process effectively.
Implement Secure Design Principles
Start by reducing potential attack surfaces. Disable unused interfaces, like USB ports or network protocols, if they aren't essential. For example, if your device doesn't need Bluetooth, disable it entirely rather than leaving it inactive but accessible.
Strengthen your defenses with strong authentication methods, like multi-factor authentication, and ensure encryption standards are top-notch (e.g., TLS 1.3+). Encrypt data both in transit and at rest. For devices like pacemakers, avoid using default credentials and integrate secure boot processes to verify firmware integrity before it runs. Use role-based access control (RBAC) to enforce the principle of least privilege, granting users and processes access only to what they need. Adding a hardware root of trust for cryptographic operations can further bolster security.
Generate a Software Bill of Materials (SBOM)
An SBOM is essentially a detailed inventory of all software components in your device. It includes open-source libraries, proprietary code, dependencies, and metadata like version numbers and suppliers. This inventory becomes critical when vulnerabilities arise, allowing for quick identification and resolution.
Create your SBOM in a standardized, machine-readable format like CycloneDX or SPDX in JSON. Automate this process using tools such as GitHub's Dependabot during the build phase. Make sure to include transitive dependencies (those indirectly linked to your software) and compare your components against resources like the CISA Known Exploited Vulnerabilities (KEV) catalog to address high-risk issues first. Industry data suggests this approach can reduce remediation times by up to 50% [6]. Keep your SBOM up-to-date throughout development, and include it in FDA 510(k) submissions.
Integrate Cybersecurity Design Inputs
Cybersecurity requirements should be treated with the same importance as other design inputs under 21 CFR 820.30. For example, requirements like "encrypt PHI with AES-256" or "enable secure over-the-air updates" should be explicitly outlined in your Design and Development Plans. These requirements must trace directly back to identified threats.
Take insulin pumps as an example - design inputs should address hazards like unauthorized access with specific controls. Document all cybersecurity hazards and their mitigations in your plans, and implement checkpoints at each development phase to verify compliance. According to FDA case studies, this structured approach can cut post-market vulnerabilities by up to 70% [6].
Verification, Validation, and Testing Checklist
Thoroughly testing your cybersecurity design is essential. The FDA mandates that you validate your device's ability to withstand potential threats before it hits the market. This isn't just a bureaucratic step - it's about proving your device can detect, resist, respond, and recover from real-world attack scenarios.
Perform Cybersecurity-Specific Testing
Your testing strategy should build on earlier risk assessments and address every identified vulnerability. It must account for multiple attack vectors. Start with vulnerability scanning to identify known CVEs in your operating system, applications, and third-party libraries. Follow this with penetration testing to simulate attacks like unauthorized access, data theft, and privilege escalation. Use fuzz testing to input malformed data into communication interfaces, exposing potential crashes, memory leaks, or buffer overflows that attackers could exploit.
Scrutinize all entry points - USB ports, serial connections, Bluetooth, Wi-Fi, and cloud APIs - and test each thoroughly. Apply static analysis (SAST) to review your source code for security flaws before execution, and dynamic analysis (DAST) to monitor how your device behaves during runtime. Boundary analysis ensures your device can handle extreme inputs without compromising security. Additionally, test critical features like authentication, authorization, and audit logging under stress to ensure they remain reliable.
Validate Cryptographic and Hardware Security Features
Ensure your cryptographic implementations meet current standards. Use NIST-validated modules with algorithms such as AES-256 or RSA-3072. Test hardware-based protections like Secure Boot and Trusted Execution Environments (TEE) to confirm they can't be bypassed through physical tampering or side-channel attacks. Cross-check your SBOM to confirm that all third-party cryptographic libraries are up-to-date and free of known vulnerabilities. Stress test cryptographic functions to verify that any failures won't endanger patient safety. These steps provide the evidence needed for your comprehensive testing documentation.
Document Testing Outcomes and Identified Risks
Record every test result, anomaly, and risk in detail. Your documentation must comply with the FDA guidance titled "Cybersecurity in Medical Devices: Quality Management System Considerations and Content of Premarket Submissions" (Docket FDA-2021-D-1158), updated on June 27, 2025. According to the FDA, "These recommendations are intended to promote consistency, facilitate efficient premarket review, and help ensure that marketed medical devices are sufficiently resilient to cybersecurity threats" [1].
Maintain a traceability matrix that links each test result to its corresponding risk. Include all supply chain cybersecurity risks identified through your SBOM analysis. This documentation will help demonstrate to the Center for Devices and Radiological Health (CDRH) that your device complies with Section 524B requirements for cyber devices.
Documentation and Labeling Requirements Checklist
When submitting your pre-market package, make sure to include thorough documentation that highlights your device's cybersecurity measures, as outlined by the FDA under Section 524B. The FDA guidance (FDA-2021-D-1158) specifically states: "This document provides FDA's recommendations to industry regarding cybersecurity device design, labeling, and the documentation that FDA recommends be included in premarket submissions for devices with cybersecurity risk" [4]. These requirements build on prior assessments of threats and risks to present a complete cybersecurity profile.
Prepare Detailed Threat Modeling Documentation
Using earlier risk assessments as a foundation, create threat modeling documentation tailored to your device's risk level. For instance, devices with higher stakes, like implantable cardiac monitors, demand far more comprehensive documentation than lower-risk devices like wellness trackers. Document every identified threat from your asset, threat, and vulnerability analysis, along with the specific mitigations implemented. Ensure this aligns with your traceability matrix from the threat modeling process.
Develop a Comprehensive Vulnerability Management Plan
A strong vulnerability management plan is essential for maintaining security throughout the device's lifecycle. This plan should detail how you'll monitor emerging threats, address newly identified CVEs within your SBOM components, and apply security patches. Specify update methods - whether over-the-air (OTA), manual, or cloud-based - and outline timelines for resolving critical vulnerabilities. Additionally, explain how you'll communicate security updates to both healthcare providers and patients.
Provide Clear Cybersecurity Feature Labeling
Clearly label cybersecurity features for end users. This includes instructions on backup and restore procedures, software update processes, authentication protocols, and user responsibilities. Transparent labeling helps healthcare organizations integrate your device into their existing security frameworks while meeting their own risk management requirements.
Using Censinet RiskOps™ for Pre-Market Cybersecurity

Censinet RiskOps™ builds on established threat modeling and risk assessment practices, making the process smoother and more efficient. Managing FDA pre-market cybersecurity requirements often involves juggling extensive documentation and coordinating with numerous stakeholders. Censinet RiskOps™ simplifies this by centralizing workflows tailored specifically for healthcare organizations dealing with medical device cybersecurity. This approach ensures that automated documentation and collaborative risk management align seamlessly with early pre-market cybersecurity steps and compliance with Section 524B requirements.
Accelerate Risk Assessments and Streamline Threat Modeling
Censinet RiskOps™ automates risk assessments based on industry standards like NIST CSF 2.0 and HHS Healthcare and Public Health Sector Cybersecurity Performance Goals (HPH CPGs). By leveraging Censinet GRC AI™, the platform delivers AI-driven insights to identify attack surfaces, adversary motivations, and critical assets - key elements required by FDA design guidelines. It also creates automated action plans to address security control gaps, assigning tasks to internal stakeholders with real-time tracking. This not only reduces the time spent preparing threat modeling documentation but also ensures accuracy and thoroughness for pre-market submissions.
Improve Collaboration and Benchmarking
The platform fosters collaboration between manufacturers and healthcare organizations through its cloud-based design, helping meet cybersecurity requirements more effectively. It maps enterprise assessments to current regulatory standards, making compliance easier. Additionally, it allows organizations to compare their cybersecurity maturity against industry peers using data from the 2026 Healthcare Cybersecurity Benchmarking Study. This feature helps pinpoint gaps, prioritize improvements, and justify investments to stakeholders. It’s especially useful when documenting risk levels and mitigation strategies for devices with different risk profiles.
Accelerate Assessments with Censinet AI
Censinet AI complements these efforts by speeding up technical assessments. It automates the completion of security questionnaires, summarizes vendor evidence and documentation, and captures critical product integration details. While automation handles repetitive tasks, human oversight remains central through configurable rules, ensuring that key decisions are always managed by risk teams. This balance allows for efficient management of complex risks throughout the pre-market cybersecurity process.
Conclusion
Pre-market cybersecurity in healthcare requires a combination of threat modeling, secure design, thorough testing, and detailed documentation. To meet FDA requirements and protect patient safety, healthcare organizations must take several critical steps: conduct detailed asset and vulnerability assessments, apply secure design principles, create Software Bills of Materials (SBOMs), validate cryptographic functionalities, and establish clear vulnerability management plans.
The importance of these measures cannot be overstated. In 2023, cybersecurity incidents in healthcare increased by 45%, leading to breaches of 22 million patient records. Additionally, 2024 saw 15 FDA cybersecurity-related recalls. Proper pre-market risk management can address up to 80% of known vulnerabilities before medical devices are deployed in clinical environments [7].
Tools like Censinet RiskOps™ simplify this process, helping healthcare organizations meet FDA requirements more efficiently.
To implement these measures effectively, organizations should adopt a "Do-Confirm" approach. This involves identifying 5–9 critical high-risk steps per section, assigning clear responsibilities, and incorporating verification points during design reviews and pre-submission audits. Testing these checklists with device engineers and maintaining version control with documented updates ensures continuous refinement. Each step contributes to a cohesive strategy for securing medical devices.
Taking a proactive stance on pre-market cybersecurity is essential to protecting patients from cyber threats. By following this structured approach and utilizing specialized tools like Censinet RiskOps™, healthcare organizations can better navigate the complexities of FDA compliance with confidence.
FAQs
What devices qualify as a “cyber device” under FDA Section 524B?
A "cyber device", as defined by FDA Section 524B, refers to a medical device that meets these specific conditions:
- It includes software that the manufacturer has validated, installed, or authorized.
- It connects to the internet or other networks, whether directly or indirectly.
- It has features that could make it susceptible to cybersecurity risks.
These guidelines are designed to pinpoint devices that need strong cybersecurity protections.
What’s the minimum SBOM detail the FDA expects in a premarket submission?
The FDA mandates that an SBOM (Software Bill of Materials) in premarket submissions must include several key elements: supplier details, component versions, dependencies, timestamps, and vulnerability assessments. Accepted formats for submission are SPDX and CycloneDX. These requirements aim to promote transparency and enhance the security of connected medical devices.
How do I prove my cybersecurity testing covers every identified risk?
To showcase thorough cybersecurity testing, it's critical to document how each identified risk is addressed. This involves using threat modeling, risk assessments, and testing activities such as vulnerability scanning and penetration testing to mitigate risks effectively.
Key Steps to Ensure Risk Mitigation
-
Link Risks to Controls and Mitigation Strategies
Each identified risk should be mapped to specific controls and mitigation strategies. For example, if a risk involves unauthorized access, link it to access control measures like multi-factor authentication or role-based access controls. -
Perform Structured Testing Activities
Testing activities like vulnerability assessments and penetration tests help verify risk reduction. Document these tests and their results, providing evidence of identified vulnerabilities and how they were addressed. -
Ensure Traceability
Maintain clear traceability by linking risks to their corresponding controls, mitigation efforts, and test outcomes. This ensures a transparent process and makes it easier to demonstrate compliance with security standards. -
Use Frameworks with Defined Acceptance Criteria
Structured frameworks, such as NIST or ISO 27001, provide a clear path for assessing and mitigating risks. Include acceptance criteria to define what constitutes an acceptable level of risk and provide evidence that these criteria have been met.
Providing Evidence of Risk Reduction
It's essential to show that all risks have been addressed and verified. This can include test reports, logs, and documented results from the risk assessments. By combining these elements, you create a comprehensive record that demonstrates due diligence and effective risk management.

