Healthcare organizations face a growing challenge: protecting sensitive patient data while ensuring seamless access for authorized users. Digital identity solutions are now key to addressing this issue, offering secure ways to verify identities, control access, and share data across platforms. Here's what you need to know:
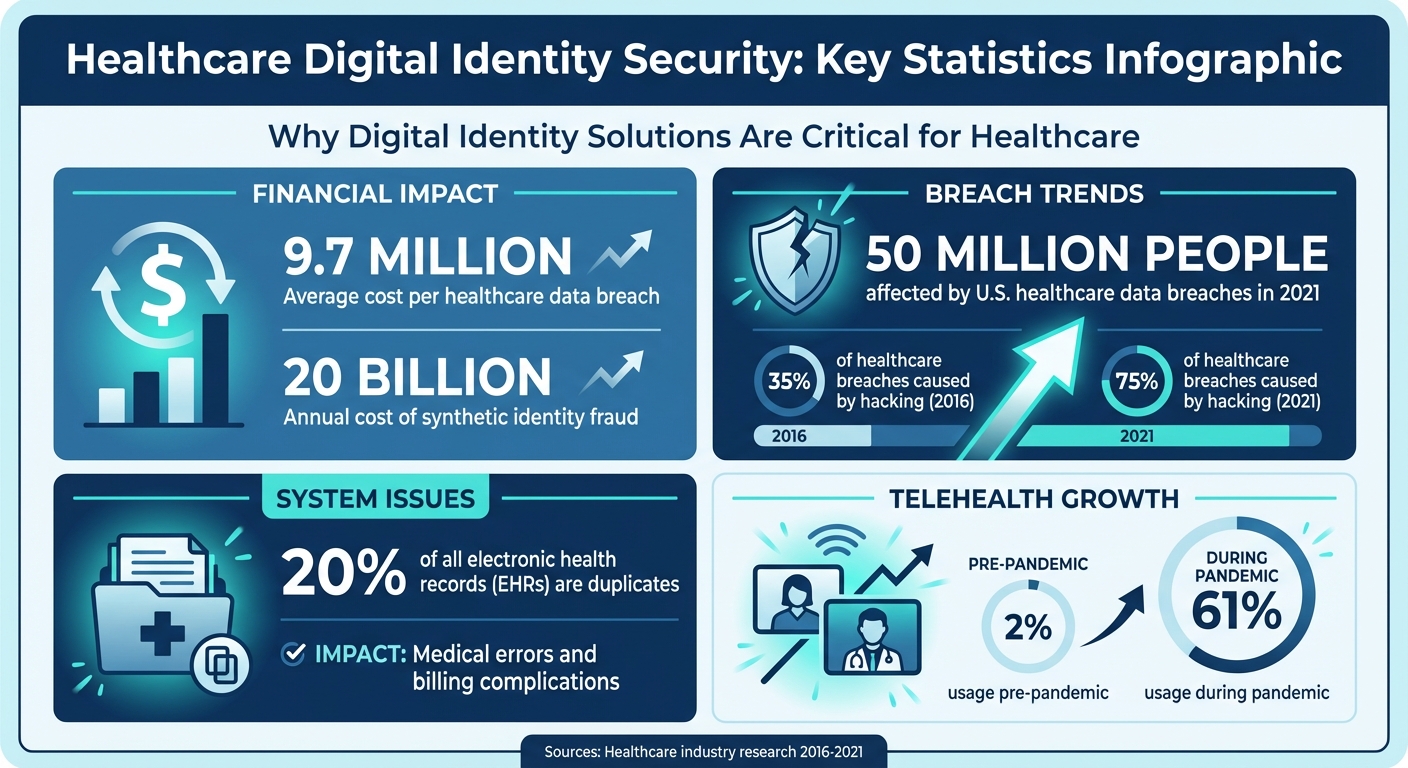
With healthcare data breaches costing an average of $9.7 million per incident, implementing strong digital identity solutions isn't optional - it's a necessity. The integration of advanced tools, such as Censinet RiskOps™, further streamlines risk management, automates processes, and strengthens security.
This article explores how digital identity works, its core components, and the challenges healthcare organizations face in safeguarding patient data.
Healthcare Data Breach Statistics and Digital Identity Security Impact
Digital ID Flips the Script on Patient Data Ownership
sbb-itb-535baee
Core Elements of Digital Identity in Healthcare
In healthcare, digital identity hinges on three key components: strong authentication, precise access controls, and secure data sharing. These elements work together to safeguard patient information and close gaps in data protection.
Authentication Methods to Block Unauthorized Access
Traditional passwords are increasingly being phased out in healthcare due to their security flaws. Instead, biometric authentication - like facial recognition, fingerprint scans, and iris recognition - has become a core defense. These physical traits are extremely difficult to replicate, making them a reliable barrier against unauthorized access[4][8]. To strengthen this further, technologies like ISO 30107-certified liveness detection ensure real-time user actions (e.g., blinking or smiling) are required, effectively countering deepfakes and static images[4][8].
Multi-factor authentication (MFA) adds another layer of protection by combining methods like SMS codes, app-based verification, and biometrics[6]. For a more seamless experience, adaptive authentication uses risk scoring to flag unusual login behavior, only increasing security measures when necessary. This strikes a balance between user convenience and robust protection.
"Healthcare data's unique sensitivity makes the front-end verification process even more critical, as any failure to accurately confirm identity can lead to unauthorized parties gaining access to personal health records." - ID Dataweb
Identity proofing takes security a step further by matching live selfies to government-issued IDs, such as mobile driver’s licenses, and cross-referencing authoritative databases[4][8]. This approach not only helps combat synthetic identity fraud, which costs an estimated $20 billion annually, but also reduces duplicate records - an issue affecting about 20% of all electronic health records (EHRs). Duplicate records can lead to medical errors and billing complications[4].
Once authentication is secured, the next challenge is defining who can access what data.
Role-Based Access Control (RBAC) Through IAM
Identity and Access Management (IAM) systems ensure that access to patient data is strictly controlled. Unlike traditional IAM frameworks designed for employees, healthcare organizations now rely on Customer Identity and Access Management (CIAM) to handle millions of patients using personal devices[6].
Role-Based Access Control (RBAC) enforces boundaries by granting access based on roles. For example, a billing specialist can’t view clinical notes, and a nurse in one department can’t access records from another without proper clearance. This minimizes insider and third-party threats and limits the damage caused by compromised credentials. RBAC also supports delegated access, allowing caregivers or proxies to manage health information for patients who are elderly or have disabilities[6].
To enhance security and comply with regulations, healthcare organizations are adopting standards like NIST Identity Assurance Level 2 (IAL2) and Authenticator Assurance Level 2 (AAL2) for patient portals[7][9]. These standards provide clear guidelines for verification processes while maintaining ease of use.
With access tightly controlled, the next priority is ensuring secure data sharing across systems.
Secure Data Sharing Between Providers
As patients move between specialists, hospitals, and telehealth platforms, their data must travel securely alongside them. Portable digital credentials allow patients to use a single, verified identity across multiple providers, eliminating the need for multiple accounts[7][9]. The CARIN Alliance promotes this patient-centered model, giving individuals control over how and when their data is shared[7].
FHIR (Fast Healthcare Interoperability Resources) APIs form the technical backbone for this interoperability, enabling verified identities to integrate seamlessly across different healthcare systems[9]. Encryption ensures data remains secure during these transfers.
The importance of secure sharing is underscored by the scale of breaches: in 2021, nearly 50 million people in the U.S. were affected by healthcare data breaches, with hacking responsible for nearly 75% of incidents - up from 35% in 2016[7]. The rapid rise of remote care, which jumped from 2% usage pre-pandemic to 61% during the crisis, has further expanded the attack surface[8].
Challenges in Protecting Patient Data
Healthcare data breaches come with hefty consequences - financial losses, damaged reputations, and regulatory penalties. On average, these breaches cost a staggering $9.7 million, making them a serious concern for healthcare organizations.
Data Breach Risks and Vulnerabilities
Healthcare systems face persistent threats like credential theft and insider attacks. The widespread adoption of cloud platforms, electronic health records (EHRs), and telemedicine has expanded the potential points of attack, including vulnerable medical devices. This broader digital footprint leaves labs, hospitals, insurance providers, and even government databases more exposed to cyber risks[2]. To counter these threats, advanced digital identity protections are critical.
Balancing Interoperability with Security
Efficient data sharing is vital in healthcare, but ensuring this exchange happens securely is a tough balancing act. Frameworks like GS1 identifiers and HL7 FHIR promote secure data sharing, but integrating these standards with strong access controls isn’t straightforward[2]. On top of that, outdated verification processes can hinder patient access while also raising privacy concerns.
Compliance with Changing Regulations
Digital identity systems must incorporate secure authentication and access controls to align with various regulatory demands. However, navigating these overlapping frameworks is no small feat. For instance:
Managing sensitive healthcare data under these complex and sometimes conflicting regulations makes implementing secure digital identity systems a resource-heavy challenge[3].
How Censinet RiskOps™ Strengthens Digital Identity Security
Managing digital identity risks in healthcare is no small task. Threats evolve quickly, and keeping up requires tools that can adapt just as fast. That's where Censinet RiskOps™ steps in, offering a unified platform that connects IT, biomedical, supply chain, and research departments to streamline risk management.
Faster Risk Assessments
Traditional risk assessments can stretch on for weeks, leaving organizations vulnerable in the meantime. Censinet RiskOps™ speeds up the process using delta-based reassessments. Instead of reviewing all vendor data from scratch, it focuses only on changes in responses, cutting reassessment times to less than a day on average[10]. Plus, its Digital Risk Catalog™ provides instant access to over 50,000 pre-assessed vendors and products, making it easier to evaluate digital identity solutions efficiently[10].
Terry Grogan, CISO at Tower Health, shared how this efficiency transformed their operations:
"Censinet RiskOps allowed 3 FTEs to go back to their real jobs! Now we do a lot more risk assessments with only 2 FTEs required."
Automated Cybersecurity Workflows
Manually tracking security gaps is not only time-consuming but also risky - delays can give attackers a window of opportunity. Censinet RiskOps™ eliminates these delays by automating key workflows, including audit trails, access revocation, and compliance reporting. The platform sends real-time alerts for threats like credential theft and flags issues such as missing Business Associate Agreements (BAAs) or vulnerabilities like Log4j across the vendor portfolio. Automated Corrective Action Plans (CAPs) ensure teams can address these gaps quickly and effectively[10].
This level of automation fosters a more seamless and collaborative approach to managing digital identity risks, saving time while enhancing security.
Collaborative Risk Management for HDOs
Digital identity security isn't just an IT issue - it’s a team effort involving clinical staff, vendors, and leadership. Censinet RiskOps™ acts as a hub for collaboration, enabling healthcare delivery organizations (HDOs) and third-party vendors to share cybersecurity data efficiently. The platform’s 1-Click Evidence Sharing feature allows vendors to complete standardized questionnaires once and share them instantly with unlimited customers, ensuring data stays current[10].
With over 100 provider and payer facilities participating in the Censinet Risk Network, organizations can benchmark their cybersecurity efforts against peers. This collaborative environment helps identify shared vulnerabilities in areas like device authentication and supply chain risks[10].
Best Practices for Implementing Digital Identity Solutions
Creating an effective digital identity strategy requires careful planning. It should address risks, accommodate future growth, and establish secure, unified practices.
Conduct Regular Risk Assessments
Hoping for the best isn't a plan. Regular risk assessments - ideally every quarter or after major system updates - are essential for spotting issues before they escalate. Keep an eye on unauthorized access, use AI to detect anomalies, and review healthcare cybersecurity benchmarking and compliance audits thoroughly.
Adopt Identity and Access Management (IAM) frameworks with built-in audit trails for continuous oversight. Incorporating standards like HL7 FHIR ensures that security measures align with data-sharing needs and regulatory requirements[2][3]. The aim is clear: identify threats early, fix vulnerabilities quickly, and stay HIPAA-compliant.
This proactive approach sets the stage for implementing technologies that can grow alongside your organization.
Adopt Scalable, Compliant Technologies
Your digital identity solutions need to grow with you. Scalable technologies like multi-factor authentication (MFA), biometrics, and Zero Trust Architecture provide ongoing verification and adaptability. Look for tools with features like end-to-end encryption, liveness detection to block spoofing, and adaptive role-based access control that adjusts as your organization evolves.
Real-world examples show that dynamic identity verification can reduce fraud, cut down errors, and simplify patient onboarding and access to electronic health records. Choosing technologies that balance scalability with compliance ensures your security measures can keep up with changing regulations and organizational needs.
But even the best technology won't work without a knowledgeable team.
Train Staff on Secure Practices
Technology isn't enough if your team doesn't know how to use it securely. Annual training sessions, supplemented by quarterly refreshers, help staff identify threats like phishing, properly use MFA and biometrics, understand role-based access control, and respond to access log alerts[2][3]. Since human error often leads to breaches, ongoing education is essential.
Training should be practical, not just theoretical. Staff who can spot credential theft, confidently use biometric systems, and report anomalies become a critical part of your defense. The key is to integrate these practices into daily routines rather than limiting them to occasional compliance checks.
Conclusion
Digital identity serves as the backbone for safeguarding patient data in today's interconnected healthcare environment. With the steep financial and reputational costs of data breaches, healthcare organizations can no longer rely on outdated authentication methods. By adopting digital identity frameworks that integrate multi-factor authentication, biometrics, and Zero Trust Architecture, organizations can tackle key vulnerabilities like unauthorized access, credential theft, and compliance risks.
However, the challenge isn't just about deploying advanced authentication tools - it’s also about managing the complexity that comes with integrating these solutions across various vendors, clinical applications, and medical devices. This is where Censinet RiskOps™ steps in. Designed specifically for healthcare delivery organizations, it simplifies risk assessments, automates cybersecurity workflows, and supports collaborative risk management. As the first cloud-based risk exchange tailored for healthcare, it offers the visibility and control needed to safeguard PHI while adhering to HIPAA requirements[11].
Emerging technologies are also paving the way for even stronger data protection measures. Innovations like AI-driven verification, blockchain-based patient-controlled identities, and dynamic risk-based authentication are transforming how healthcare organizations secure access to sensitive information[2][5]. By combining these advancements with established digital identity frameworks and solutions like Censinet RiskOps™, healthcare organizations can stay ahead of evolving threats while meeting regulatory demands, including those outlined in the 21st Century Cures Act.
FAQs
What’s the difference between authentication and identity proofing?
In the world of digital identity management, identity proofing plays a crucial role during account setup. This process verifies a person’s identity by using documents such as government-issued IDs or biometrics, helping to prevent fraudulent activities. Importantly, this step happens just once during the onboarding phase.
On the other hand, authentication is an ongoing process. It ensures a user’s identity is confirmed every time they access a system. This is typically done through methods like passwords, multi-factor authentication (MFA), or biometrics.
Together, these processes work to safeguard sensitive patient data and ensure compliance with healthcare regulations, such as HIPAA.
How does RBAC limit what staff can see in EHRs?
RBAC, or Role-Based Access Control, limits staff access to Electronic Health Records (EHRs) by assigning permissions based on their specific job roles. This approach ensures that only the right personnel can view or interact with certain patient data. By restricting access in this way, RBAC helps reduce the chances of data breaches, making it easier to maintain HIPAA compliance. It’s a practical way to enhance data security while meeting healthcare's strict regulatory standards.
How can providers share data via FHIR without risking PHI?
Providers can share data securely using FHIR by leveraging secure APIs equipped with strong authentication methods like OAuth 2.0 and SMART on FHIR. To protect patient health information (PHI) and meet healthcare regulations, it's crucial to follow key practices such as:
These steps are essential for maintaining the integrity and security of sensitive healthcare data.
Related Blog Posts
- HIPAA Compliance and Biometric Data in Clinical Apps
- How IAM Integration Prevents Healthcare Data Breaches
- Telehealth Security: Identity Proofing vs. Authentication
- HIPAA Standards for Digital Identity
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"What’s the difference between authentication and identity proofing?","acceptedAnswer":{"@type":"Answer","text":"<p>In the world of digital identity management, <strong>identity proofing</strong> plays a crucial role during account setup. This process verifies a person’s identity by using documents such as government-issued IDs or biometrics, helping to prevent fraudulent activities. Importantly, this step happens just once during the onboarding phase.</p> <p>On the other hand, <strong>authentication</strong> is an ongoing process. It ensures a user’s identity is confirmed every time they access a system. This is typically done through methods like passwords, multi-factor authentication (MFA), or biometrics.</p> <p>Together, these processes work to safeguard sensitive patient data and ensure compliance with healthcare regulations, such as HIPAA.</p>"}},{"@type":"Question","name":"How does RBAC limit what staff can see in EHRs?","acceptedAnswer":{"@type":"Answer","text":"<p>RBAC, or Role-Based Access Control, limits staff access to Electronic Health Records (EHRs) by assigning permissions based on their specific job roles. This approach ensures that only the right personnel can view or interact with certain patient data. By restricting access in this way, RBAC helps reduce the chances of data breaches, making it easier to maintain HIPAA compliance. It’s a practical way to enhance data security while meeting healthcare's strict regulatory standards.</p>"}},{"@type":"Question","name":"How can providers share data via FHIR without risking PHI?","acceptedAnswer":{"@type":"Answer","text":"<p>Providers can share data securely using FHIR by leveraging secure APIs equipped with strong authentication methods like <strong><a href=\"https://oauth.net/2/\" target=\"_blank\" rel=\"nofollow noopener noreferrer\">OAuth 2.0</a></strong> and <strong><a href=\"https://smarthealthit.org/\" target=\"_blank\" rel=\"nofollow noopener noreferrer\">SMART on FHIR</a></strong>. To protect patient health information (PHI) and meet healthcare regulations, it's crucial to follow key practices such as:</p> <ul> <li><strong>Strong access controls</strong>: Limit access to authorized users only.</li> <li><strong>Data encryption</strong>: Encrypt data both in transit and at rest.</li> <li><strong>Addressing API misconfigurations</strong>: Regularly review and fix potential vulnerabilities to prevent breaches.</li> </ul> <p>These steps are essential for maintaining the integrity and security of sensitive healthcare data.</p>"}}]}

