Key Rotation Policies for PHI Encryption
Post Summary
Encryption key rotation is a critical part of protecting sensitive healthcare data like PHI (Protected Health Information). Regularly updating encryption keys reduces the risk of data breaches, limits the impact of compromised keys, and ensures compliance with regulations like HIPAA and NIST guidelines. Here's what you need to know:
- Why It Matters: Key rotation minimizes the risk of prolonged exposure in case of a breach. It also limits the data encrypted under a single key, making attacks harder.
- Regulations: HIPAA encourages encryption and key management, while NIST provides detailed guidelines on cryptoperiods and lifecycle management. FIPS 140-3 compliance will be mandatory for new deployments by September 2026.
- Implementation: Automated tools like AWS KMS or Azure Key Vault simplify rotation. Techniques like zero-downtime rotation, lazy re-encryption, and blue-green strategies ensure uninterrupted access.
- Best Practices: Use automated rotation schedules (e.g., every 90 days), secure key storage, monitor key usage, and maintain detailed audit logs.
- Challenges: Avoid errors like prematurely retiring keys or disrupting services. Automation and testing can help mitigate these risks.
Key rotation isn't optional - it's essential for protecting PHI and meeting compliance standards. Automating the process and following best practices ensures security without interrupting healthcare operations.
Key Rotation and Management
sbb-itb-535baee
Regulatory Requirements for PHI Encryption and Key Rotation
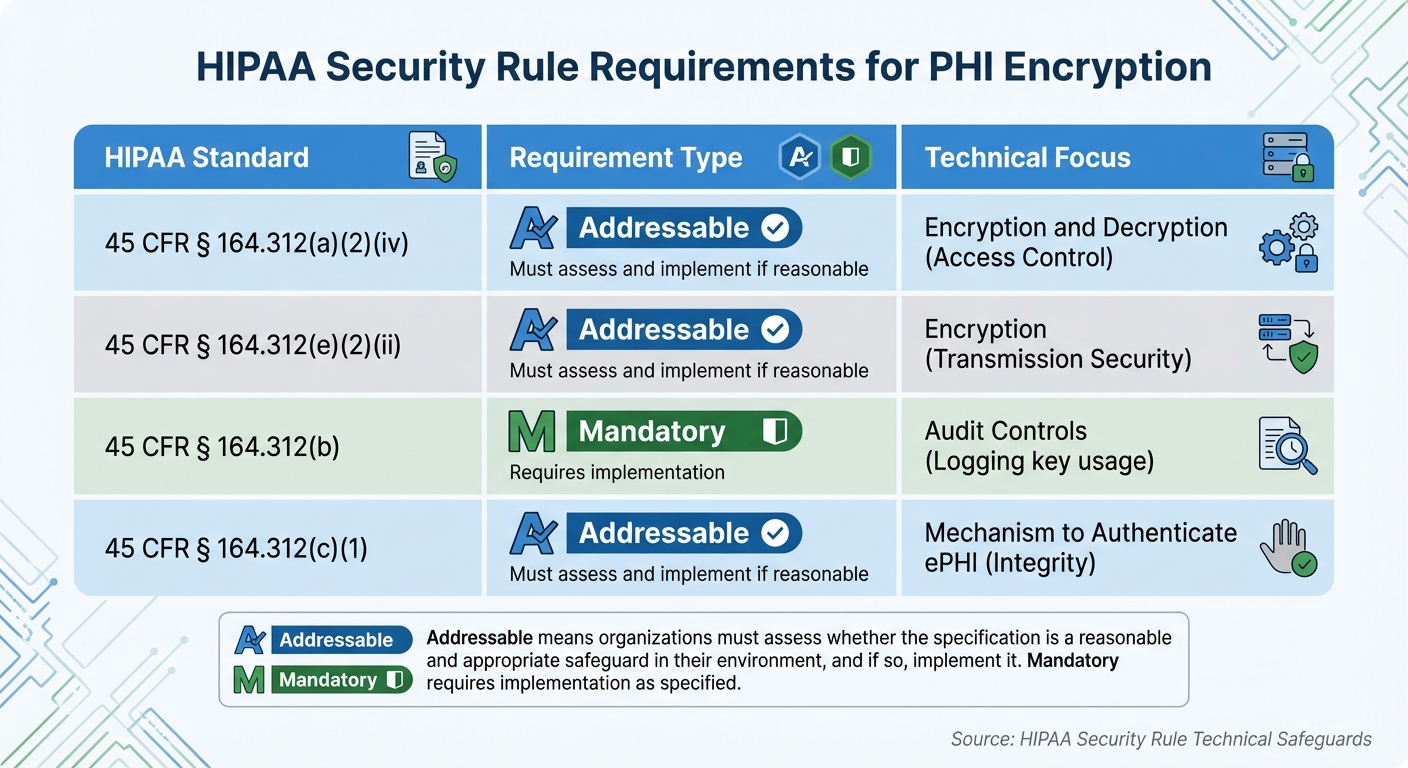
HIPAA Security Rule Requirements for PHI Encryption and Key Management
Healthcare organizations must navigate a complex web of regulations to develop compliant strategies for key rotation and encryption to protect PHI. These regulatory frameworks provide the groundwork for effective practices, as explored below.
HIPAA Requirements for Key Rotation
Under the HIPAA Security Rule, encryption is classified as "addressable." This means organizations must conduct risk assessments to decide whether encryption and key management safeguards are appropriate, though no specific rotation intervals are mandated [2][4].
HIPAA's technical safeguards emphasize encryption to secure electronic PHI (ePHI) both at rest and in transit. As Gil Vidals, CEO of HIPAA Vault, explains:
Under the HIPAA Security Rule, encryption of PHI is deemed "addressable" - meaning organizations must evaluate whether it is reasonable and appropriate given their risk environment and, if so, implement it [4].
To meet these requirements, best practices include using AES-256 encryption for data at rest and TLS 1.2 or higher for data in transit. Additionally, maintaining detailed audit trails for key access, administrative changes, and decryption events is critical to comply with HIPAA's Audit Controls [4][5].
| HIPAA Standard | Requirement Type | Technical Focus |
|---|---|---|
| 45 CFR § 164.312(a)3 | Addressable | Encryption and Decryption (Access Control) |
| 45 CFR § 164.312(e)3 | Addressable | Encryption (Transmission Security) |
| 45 CFR § 164.312(b) | Mandatory | Audit Controls (Logging key usage) |
| 45 CFR § 164.312(c)[3] | Addressable | Mechanism to Authenticate ePHI (Integrity) |
To complement HIPAA, NIST provides detailed technical guidelines to refine key management practices further.
NIST Guidelines for Key Management
NIST SP 800-57 offers a comprehensive framework for key management, divided into three parts. Part 1 covers general best practices, Part 2 focuses on policy and planning, and Part 3 addresses specific system features. The latest version, Part 1 Revision 6 (a draft published in December 2025), also includes guidance on transitioning to quantum-resistant algorithms [7].
A key aspect of NIST's guidance is the concept of the cryptoperiod, which determines when keys should be retired and replaced. Organizations are required to establish a Key Management Policy and a Key Management Practice Statement (KMPS) to outline key generation, protection, and rotation procedures [6].
NIST defines four phases in a key's lifecycle: Pre-operational, Operational, Post-operational, and Destroyed. Post-operational keys may be archived for legacy data decryption when necessary. Additionally, NIST emphasizes separating key functions, ensuring that keys used for "key establishment" are distinct from those used for "key storage", which strengthens security controls [5][7].
Additional Compliance Frameworks
Federal healthcare entities must also align with CMS policies, FIPS 140-3, and OMB directives, which enforce key rotation and updated cryptographic standards. For example:
- CMS Information Security and Privacy Policy (IS2P2) and CMS Acceptable Risk Safeguards (ARS) require policies for managing cryptographic keys and mandate regular risk assessment reviews, at least every three years or sooner if significant changes occur [5].
- FIPS 140-3 governs cryptographic module validation. By September 22, 2026, all modules must comply with FIPS 140-3, as FIPS 140-2 certifications will no longer be valid for new deployments [5]. The CMS Key Management Handbook advises:
Shared secrets, such as encryption keys and single-factor or shared passwords, should be periodically rotated to minimize the risk of unauthorized access [5].
- OMB Memorandum M-23-02 requires federal agencies to inventory cryptographic dependencies and prepare for a transition to quantum-resistant algorithms to counter future brute-force risks [5].
How to Implement Key Rotation in Healthcare Organizations
Implementing key rotation in healthcare organizations involves striking a balance between stringent security measures and uninterrupted clinical operations. Protecting sensitive patient data, or PHI, while ensuring 24/7 access to critical systems is a top priority. Here's how organizations can achieve effective key rotation without disrupting patient care or data accessibility.
Zero-Downtime Key Rotation Methods
Key versioning is a method that allows encryption keys to be rotated without causing downtime. This technique involves maintaining multiple versions of encryption keys simultaneously. New data gets encrypted with the latest key, while older data remains accessible using the specific key version stored with the encrypted information.
Bob Ertl from Kiteworks explains this concept succinctly:
Zero-downtime key rotation replaces encryption keys without service interruption, allowing users to continue accessing encrypted data throughout the rotation process. [9]
Cloud providers simplify this process by enabling seamless decryption with rotated keys, ensuring applications continue to function without requiring any code changes.
Organizations can adopt one of two main strategies for key rotation:
- Blue-Green Rotation: This approach involves maintaining two complete key sets. Traffic is gradually shifted from the old set to the new one using weighted load balancing, allowing full validation before switching over entirely.
- Canary Rotation: Keys are updated for a small subset of users or systems first, providing an opportunity to test operations before rolling out the changes organization-wide.
For re-encrypting existing data, two additional strategies are often employed:
- Lazy Re-encryption: Data is updated with the new key only when accessed, reducing operational overhead.
- Online Background Re-encryption: Background processes re-encrypt historical data without causing service interruptions.
| Strategy | Best Use Case | Key Advantage |
|---|---|---|
| Blue-Green Rotation | 24/7 high-availability services | Full validation before cutover |
| Canary Rotation | Complex enterprise environments | Limited impact if failure occurs |
| Lazy Re-encryption | Large datasets with mixed access | Minimal operational overhead |
| Online Background Re-encryption | Standardizing security across all data | No service interruption |
Automating Key Rotation
Automation plays a critical role in maintaining compliance with HIPAA and NIST guidelines by reducing the risk of human error. Tools like AWS KMS and Azure Key Vault make it easy to automate rotations. For instance, AWS KMS rotates AWS-managed keys every 365 days - a change from its previous three-year cycle as of May 2022 [8].
Because AWS KMS transparently decrypts with the appropriate key material, you can safely use a rotated KMS key in applications and AWS services without code changes. [8]
For customer-managed keys, AWS KMS allows custom rotation intervals ranging from 90 to 2,560 days (approximately 7 years) [8,14]. Similarly, Azure Managed HSM mandates a minimum rotation interval of 28 days for automatic policies [11]. When using Azure Key Vault, configuring versionless URIs ensures that services automatically refresh to the latest key version without manual intervention [12].
Automation also proves invaluable for immediate rotations, such as when a key is suspected of being compromised or when an employee with access leaves the organization [9]. For key types that don't support native auto-rotation (e.g., asymmetric or HMAC keys), serverless solutions like AWS Lambda can be triggered to create new keys and update aliases on a set schedule [13].
To ensure the process runs smoothly, organizations should monitor rotations closely. For example, checking CloudTrail logs for RotateKey events or using Azure Policy compliance scans can verify that rotations occur as planned [12]. Tracking encryption and decryption attempts during the rotation period also helps identify potential issues early, allowing for quick rollbacks if needed [9].
Using Risk Management Platforms for Key Lifecycle Tracking
Managing encryption keys effectively requires integrating key rotation into broader enterprise risk management efforts. Platforms like Censinet RiskOps™ enable healthcare organizations to track encryption key lifecycles alongside other risks, such as those related to third-party vendors, clinical systems, and medical devices. This approach ensures that key rotation aligns with overall security goals and compliance benchmarks.
Risk management platforms also help flag manual rotation requirements for imported key material, reducing the likelihood of compliance gaps. By maintaining a complete version history of cryptographic keys, these platforms ensure that older PHI remains accessible without requiring manual tracking.
For database and storage systems, these platforms can coordinate workflows to ensure zero-downtime rotations. For instance, when rotating keys for RDS databases, teams might:
- Take a snapshot of the database.
- Copy the snapshot with a new KMS key.
- Restore it to a new cluster.
- Verify the new instance.
- Decommission the old cluster.
Similarly, for large datasets stored in S3, batch operations can be used to read and rewrite objects with the new key. Documenting these workflows within a risk management platform ensures consistency and reliability across the organization. These practices lay the groundwork for establishing robust key rotation policies, which will be explored further in the next section.
Best Practices for Key Rotation Policies
Creating strong key rotation policies requires a careful balance between security and practical implementation. For healthcare organizations, this means establishing clear guidelines to safeguard PHI, ensure system uptime, and meet compliance requirements.
Setting Rotation Schedules and Documenting Policies
Key rotation schedules should align with industry standards and compliance needs. Microsoft Learn suggests a minimum rotation interval of two years, but depending on the risk level, intervals can range from 90 days to two years [10][1].
The appropriate rotation frequency depends on the type of key and its usage. Symmetric keys, often managed in cloud vaults, allow for automated, hands-free rotation, making frequent updates feasible [10][1]. On the other hand, asymmetric keys typically require manual distribution of new public key components, which may call for longer intervals [1]. For keys used in GCM mode, NIST bases its recommendations on the number of messages generated rather than elapsed time [1].
Google Cloud Documentation highlights the benefits of automation:
Automatic key rotation at a defined period, such as every 90 days, increases security with minimal administrative complexity [1].
Cloud environments, however, can introduce delays of 1 to 24 hours before all services fully recognize a new key version [10]. To address this, organizations can set up near-expiry notifications - typically 30 days before expiration - for keys that don’t support automated rotation [10].
Policies should clearly define minimum rotation intervals (e.g., 7 days from creation or expiration), specify whether triggers are time-based or volume-based, and outline procedures for various key types. Tools like Azure Policy can enforce these rules by ensuring keys rotate within a maximum timeframe, such as 730 days [10].
Securing Key Storage and Controlling Access
Once rotation schedules are in place, securing key storage and managing access are critical next steps. Centralized key management platforms, such as Azure Key Vault or Google Cloud KMS, offer a secure and organized way to store keys [10][1]. These systems support key versioning, allowing new versions to be created during rotation while retaining older versions for decrypting previously encrypted data [10].
Access control should follow the principle of least privilege. Assign specific roles, such as "Key Vault Crypto Officer", to oversee rotation policies and handle manual rotations, ensuring accountability and limiting unauthorized access [10]. Using versionless URIs can simplify application updates, as they always point to the latest key version [10]. However, older key versions must remain accessible to decrypt existing data [10][1]. Google Cloud Documentation cautions:
Destroying a key version that is still in use can cause permanent data loss [1].
If a key is compromised, it should be disabled immediately, access revoked, and data re-encrypted using the latest key. These steps help phase out outdated keys and reduce risks. Establishing these safeguards lays the groundwork for effective monitoring and auditing.
Monitoring and Auditing Key Rotation Activities
After securing key storage, continuous monitoring and auditing are essential to ensure compliance with rotation policies. Logging key usage across systems is crucial, capturing details like service access and frequency [14]. Monitoring non-human identities, such as service accounts and API keys, in real time helps identify anomalies early. Automated alerts, configured through tools like Event Grid, can notify teams 30 days before key expiration, providing ample time to address issues if automated rotation fails [10].
Governance tools should audit the entire lifecycle of each key, verifying that all keys have active rotation policies. Regular inventory checks can uncover static or outdated credentials that no longer meet security standards. As Natoma explains:
Regular audits not only ensure compliance with frameworks like PCI DSS, ISO 27001, and NIST, but also help organizations identify gaps and continuously improve their key management approach [14]. To streamline these assessments, teams can automate security questionnaires and source documentation reviews.
| Monitoring Component | Purpose |
|---|---|
| Access Logs | Track access for security and breach investigations |
| Rotation Events | Verify adherence to policies and maintain uptime |
| Usage Tracking | Identify unused keys to minimize attack surfaces |
| Compliance Scans | Ensure adherence to regulations like HIPAA, PCI DSS |
Integrating monitoring into DevOps workflows ensures security policies are followed throughout deployment. However, in cloud environments, a detection lag of 1 to 24 hours during key rotation is possible as services update to the new key version [10]. Regularly testing and refining manual rotation processes is essential to keep systems resilient in case of a security event [1].
Common Challenges and Solutions
Even with effective policies, healthcare organizations face hurdles when implementing key rotation. Identifying these challenges and addressing them head-on is crucial to safeguarding PHI while minimizing operational disruptions. Below, we dive into key management mistakes, operational challenges, and compliance issues, along with actionable solutions to tackle them.
Preventing Key Management Errors
Before retiring any encryption key, ensure no data still relies on it for decryption [1]. This means keeping older key versions active until all associated data has been either re-encrypted or deemed unnecessary [1]. Bob Ertl from Kiteworks highlights the importance of automation in this process:
Automated key rotation eliminates human error, ensures consistent adherence to rotation schedules, and scales to manage hundreds or thousands of encryption keys across enterprise infrastructure [9].
Switching from manual to automated key rotation significantly reduces the likelihood of delays and ensures adherence to rotation timelines. Incorporating Hardware Security Modules (HSMs) with FIPS 140-3 validation also guarantees that the keys used meet stringent cryptographic standards [9].
Reducing Operational Disruptions
Proper planning is essential to avoid service interruptions during key rotation. The process typically involves creating a new key version while retaining older ones for decryption purposes [1]. This ensures that older PHI remains accessible, preventing downtime. However, asymmetric keys can complicate matters, as they often require manual steps, like distributing new public keys to applications, which increases the risk of disruptions [1].
To minimize these risks, organizations should test their rotation procedures in simulated environments that mimic production systems and data loads. This helps identify potential issues before implementing changes in live environments [9]. For large-scale data re-encryption, techniques like "lazy re-encryption" (encrypting data only when accessed) or background batch processing can ease the strain on systems and meet compliance requirements [9]. Additionally, having a rollback plan in place ensures that previous key versions can be restored quickly if a rotation fails, maintaining both data accessibility and system stability [9]. Continuous monitoring and automation further reduce the potential for compliance gaps.
Closing Compliance Gaps
Ongoing monitoring and automation play a critical role in addressing compliance requirements. Key rotation is no longer optional under regulations like PCI DSS, HIPAA, and CMMC [9]. For example, HIPAA mandates regular reviews and updates of encryption mechanisms, while PCI DSS requires cryptographic keys to be rotated at least annually, with quarterly rotations advised for highly sensitive data [9].
Platforms like Censinet RiskOps™ help healthcare organizations monitor risks in real time by connecting with a network of over 50,000 vendors and products [15]. This system also provides cybersecurity benchmarking, enabling organizations to measure their preparedness against industry standards. As Brian Sterud, CIO at Faith Regional Health, explains:
Benchmarking against industry standards helps us advocate for the right resources and ensures we are leading where it matters [15].
Automated audit logs are another key tool, documenting key generation, deployment, and re-encryption activities to meet compliance audit requirements. Emergency triggers for immediate key rotation - such as those needed during employee departures or potential security breaches - allow organizations to respond swiftly to emerging threats [9].
Conclusion
Key Takeaways for Healthcare Leaders
Key rotation isn't just a best practice - it's a requirement under HIPAA, NIST SP 800-57, and PCI DSS to safeguard Protected Health Information (PHI) from prolonged vulnerability. Regularly scheduled key rotation minimizes exposure by confining risks to a single cryptoperiod, ensuring compliance with these regulations.
For highly sensitive PHI, monthly key rotations are ideal, with quarterly rotations as the bare minimum. More frequent rotations shrink the attack surface by reducing the amount of data encrypted with each key. Automating this process eliminates delays caused by shifting priorities, ensuring consistent execution even as organizations scale to manage thousands of keys. Key versioning is equally critical, allowing historical data to remain accessible with older keys while new keys secure current information. Emergency protocols for urgent rotations and lazy re-encryption (updating data only when accessed) help maintain security without interrupting day-to-day operations [9].
These strategies combine to provide strong PHI protection while aligning operational processes with compliance demands.
How Censinet Supports Key Rotation Management
Censinet RiskOps™ takes these principles and turns them into actionable practices, ensuring your key rotation strategy is both efficient and compliant. The platform empowers healthcare organizations to implement and oversee key rotation policies as part of their broader cybersecurity efforts. As previously mentioned, automation and compliance with regulatory standards are essential for effective key rotation.
With Censinet RiskOps™, you gain real-time risk monitoring across your entire ecosystem, along with tools to benchmark your key management practices against industry standards. This helps identify potential compliance gaps before auditors do. The platform’s automated workflows and centralized command center provide visibility into encryption key lifecycles, allowing you to track rotation schedules, document compliance, and generate audit logs for HIPAA and other regulatory requirements. By integrating key rotation management with third-party risk assessments and enterprise-wide risk tracking, Censinet RiskOps™ ensures your encryption strategy stays strong as your organization scales.
FAQs
How do we choose a safe key rotation interval for PHI?
To determine an appropriate key rotation interval for PHI (Protected Health Information), it’s important to strike a balance between maintaining security and ensuring smooth operations. Rotating keys regularly - commonly every 90 to 180 days - helps reduce the risk posed by outdated or compromised keys. Automating this process can simplify compliance with regulations such as HIPAA and PCI DSS.
A solid key management policy should outline not just rotation schedules but also secure methods for key generation, storage, and eventual retirement. Tailor the rotation frequency based on risk assessments and the unique requirements of your organization.
How can we rotate keys without downtime or data loss?
To rotate encryption keys without causing downtime or risking data loss, healthcare organizations need to follow a careful process. First, a new encryption key should be securely generated. Then, systems must be updated to start using the new key while still keeping the old key active during the transition. This ensures uninterrupted access to encrypted data.
Using tools like automated key rotation protocols and hardware security modules (HSMs) can make the process smoother and more secure. It's also smart to schedule key rotations during planned maintenance windows to minimize any potential disruptions. Always have fallback options in place to ensure data remains encrypted and accessible throughout the entire process.
What should we log to prove key rotation compliance?
To ensure compliance with key rotation policies, it's crucial to log specific details for each rotation. These include:
- Date and time: Record the exact date and time when the key rotation occurred.
- Identity: Document who or what system performed the rotation.
- Keys involved: Specify which keys were rotated.
- Reason for rotation: Note why the rotation was necessary (e.g., scheduled update, security concerns).
Make sure these logs are stored securely and designed to be tamper-proof. This helps maintain their integrity and supports compliance with regulatory requirements.


