NIST Cybersecurity Framework for Healthcare: Overview
Post Summary
The NIST Cybersecurity Framework is a set of guidelines, standards, and practices developed by the National Institute of Standards and Technology that helps organizations manage and reduce cybersecurity risks through six core functions, and healthcare uses it because it complements HIPAA by not only defining what needs protection but providing structured guidance on how to protect it, with adopters reporting up to 66% smaller increases in cyber insurance premiums.
The six functions are Govern covering cybersecurity strategy and PHI management policies, Identify covering asset cataloging and third-party vendor risk evaluation, Protect covering encryption and multi-factor authentication, Detect covering continuous monitoring of EHR systems for unauthorized access, Respond covering incident response plans for ransomware and other threats, and Recover covering restoration of patient data from secure backups to ensure care continuity.
Implementation Tiers range from Tier 1 (Partial), where risk management is informal and reactive, to Tier 4 (Adaptive), where practices evolve based on lessons learned and predictive insights, with most healthcare organizations starting between Tiers 1 and 2 and targeting Tier 3 (Repeatable) as a practical goal, since not every organization needs to aim for Tier 4 and progression should be driven by risk profile and cost-benefit analysis rather than ambition.
Organizational Profiles allow healthcare organizations to create a Current State Profile documenting existing security measures and a Target State Profile reflecting desired security posture, with the gap between them providing a prioritized roadmap for improvement that can also serve as a communication tool for CISOs explaining cybersecurity investment decisions to stakeholders and boards.
HIPAA defines what safeguards are legally required while the NIST CSF provides the operational blueprint for how to implement them, with 68% of US hospitals incorporating CSF elements into their HIPAA and HITECH compliance strategies and CSF-aligned organizations able to cross-map controls across frameworks to reduce duplicate work, strengthen regulatory defensibility, and simplify third-party vendor risk assessments across the business associate ecosystem.
Healthcare organizations adopting the NIST CSF report up to 66% smaller increases in cyber insurance premiums compared to non-adopters, faster incident detection through structured response processes, reduced financial exposure from a $9.77 million average breach cost that the industry has sustained for 14 consecutive years, and improved board-level communication through the framework's common cybersecurity language that bridges technical teams and executive leadership.
The NIST Cybersecurity Framework (CSF) helps healthcare organizations manage cybersecurity risks and protect sensitive patient data. With cyber threats rising - 78% of healthcare organizations reported incidents in a year - only 44% meet NIST standards, leaving many vulnerable. The CSF bridges the gap between HIPAA's regulatory requirements and actionable security practices, offering a structured approach to safeguard systems, reduce risks, and improve communication between technical teams and executives.
Key points:
NIST Adoption for Healthcare
Adopting this framework helps organizations focus on measuring what matters for cybersecurity to protect patient safety.
sbb-itb-535baee
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework (CSF) is a set of guidelines, standards, and practices created by the National Institute of Standards and Technology. It's designed to help organizations manage and minimize cybersecurity risks effectively [2][3]. Originally introduced in 2014 for critical infrastructure sectors, the framework has evolved over time. The upcoming version 2.0 (2024) is intended to support organizations of all sizes, across different industries, and at varying levels of cybersecurity readiness [2].
"It offers a taxonomy of high-level cybersecurity outcomes that can be used by any organization - regardless of its size, sector, or maturity - to better understand, assess, prioritize, and communicate its cybersecurity efforts." - NIST
One of the framework's key strengths is its adaptability. It allows organizations to align their cybersecurity strategies with their unique business goals and risk tolerance [1][5]. Adoption rates highlight its impact: within a year of its launch, 30% of U.S. organizations were already using it. By 2017, 95% of advanced healthcare organizations with dedicated security teams had implemented it [1][5].
The healthcare sector, which faces significant cybersecurity challenges, benefits greatly from the CSF. With the average cost of a ransomware attack in healthcare reaching $3.2 million and 93% of organizations in the sector experiencing phishing attacks, the need for robust security measures is clear [3]. The CSF complements HIPAA by not only defining what needs protection but also offering guidance on how to protect it [5]. Healthcare organizations using the CSF see tangible benefits, including 66% smaller increases in insurance premiums compared to those that do not adopt it [1].
Another advantage of the framework is its ability to establish a common language for cybersecurity. This shared vocabulary bridges the gap between technical teams and non-technical executives, making it easier to assess current security measures, set future goals, identify areas for improvement, and communicate risks effectively to both internal and external stakeholders [2][3]. This clear communication is essential, especially in sectors like healthcare, where the practical application of the CSF can directly safeguard patient data and critical systems. This application will be explored further in the next section.
Core Components of the NIST Cybersecurity Framework
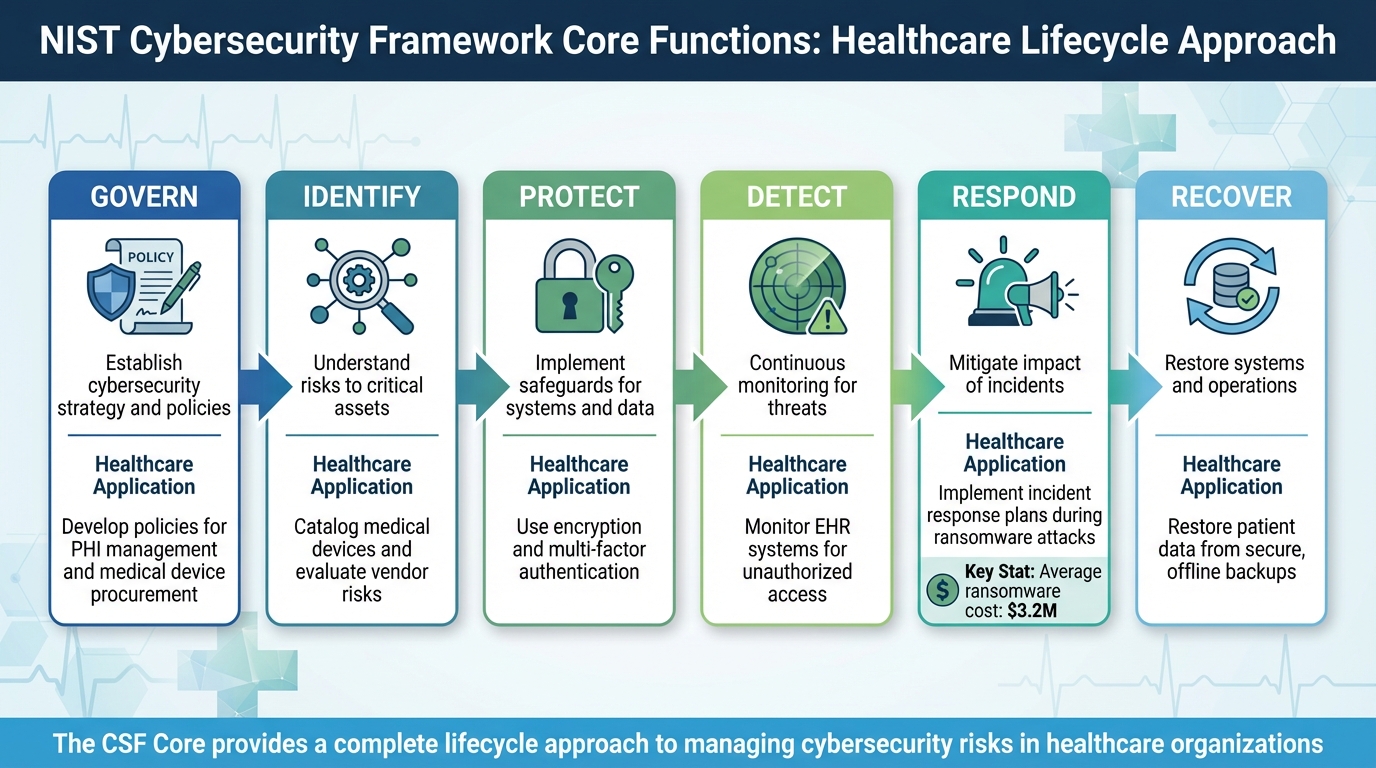
NIST Cybersecurity Framework Core Functions for Healthcare
The NIST Cybersecurity Framework (CSF) is built around three key elements: the Framework Core, Implementation Tiers, and Profiles. These components help healthcare organizations shape their security strategies based on their unique risks, resources, and regulatory requirements.
The Framework Core
The Framework Core consists of six functions that span the entire cybersecurity lifecycle. In 2024, NIST CSF 2.0 introduced a new function, Govern, which complements the original five: Identify, Protect, Detect, Respond, and Recover [2]. Each function is further broken down into Categories and Subcategories, creating a clear structure that fosters collaboration across clinical, IT, and administrative teams [6].
"The CSF Core is forward-looking and intended to apply to future changes in technologies and environments." – NIST
The Govern function focuses on establishing the organization's cybersecurity strategy, policies, and risk management framework. For healthcare, this means embedding cybersecurity into everyday operations, ensuring systems and patient data are safeguarded in alignment with the organization’s mission [2].
The Identify function emphasizes understanding risks to critical assets like Protected Health Information (PHI), connected medical devices (IoT), and supply chains. This involves cataloging all medical devices and evaluating third-party vendor risks to map potential vulnerabilities [2][3].
Protect ensures safeguards are in place, such as encrypting data both at rest and in transit, and implementing access controls like multi-factor authentication (MFA) to secure sensitive information and systems [2][3].
Detect involves continuous monitoring to spot potential threats or breaches. For instance, healthcare organizations deploy intrusion detection systems to monitor unauthorized access to electronic health records (EHR) or detect data theft attempts [2][3].
The Respond function outlines steps to mitigate the impact of incidents. With the average cost of a healthcare ransomware attack hitting $3.2 million, having a detailed response plan minimizes service disruptions [3].
Finally, Recover focuses on restoring systems and operations after an incident. For healthcare, this often involves recovering patient data from secure backups to ensure continuity of care [2][3].
CSF Core Function
Healthcare Application
Develop policies for PHI management and medical device procurement
Catalog medical devices and evaluate vendor risks
Use encryption and multi-factor authentication
Monitor EHR systems for unauthorized access
Implement incident response plans during ransomware attacks
Restore patient data from secure, offline backups
These six functions provide a foundation for organizations to assess their cybersecurity maturity, which is elaborated further in the Implementation Tiers.
Implementation Tiers
The four Implementation Tiers - ranging from Tier 1 to Tier 4 - help organizations evaluate their cybersecurity maturity. These tiers guide healthcare providers in determining whether their current risk management strategies are adequate for their threat landscape, compliance needs (like HIPAA), and business goals [2].
"Tiers should complement an organization's cybersecurity risk management methodology rather than replace it." – NIST
Not every organization needs to aim for Tier 4. Healthcare providers should focus on advancing to higher tiers only when their risk profile demands it or when a cost-benefit analysis shows the investment will effectively protect critical assets like EHR systems [2]. This approach avoids unnecessary spending while addressing key vulnerabilities [7].
Start by assessing Tier levels for a few critical systems, such as patient databases or EHR access controls. This targeted approach prevents overwhelm and builds momentum for broader implementation [7]. Define your "desired Tier" for each category to align with your risk tolerance and operational goals [2].
Profiles
Profiles make the CSF Core actionable by tailoring it to the organization’s specific needs. They allow healthcare providers to prioritize the functions, categories, and subcategories that align with their risk environment, budget, and operational context.
"The CSF Core is the complete menu of all possible cybersecurity activities. Your Profile is what you actually order based on your appetite, budget, and dietary restrictions." – Heights Consulting Group
Healthcare organizations typically create two profiles: a Current State Profile, which outlines existing security measures, and a Target State Profile, which reflects the desired security posture. Comparing these profiles highlights gaps and helps create a roadmap for improvement [2][7].
Profiles also serve as a communication tool for CISOs to explain to stakeholders how specific investments in cybersecurity protect critical outcomes like patient safety and operational stability [7]. For organizations already conducting HIPAA risk analyses, adding a column to show how NIST functions address identified risks can simplify audits and provide clear evidence for compliance [7].
How to Apply the NIST CSF in Healthcare
Incorporating the NIST Cybersecurity Framework (CSF) into healthcare security programs can complement HIPAA compliance efforts, strengthening both technical and administrative safeguards [4]. The framework’s flexibility allows organizations of all sizes - from small clinics to large hospital systems - to adapt it to their needs while adhering to its core principles [8].
"You need HIPAA to remain legal. You need NIST to remain operational." – Compass MSP
To move beyond a mere "check-the-box" approach to cybersecurity, healthcare organizations can follow three key steps: assess their current cybersecurity state, create a detailed action plan, and monitor progress continuously [8]. These steps align compliance requirements with practical security improvements.
Step 1: Assess Your Current Cybersecurity State
Start by creating a Current State Profile that documents your existing security measures across all six NIST functions. A critical part of this process is mapping out all essential assets in your environment [8].
"You cannot protect what you do not know you have." – Compass MSP
Evaluate your maturity level using NIST's Implementation Tiers, which range from Tier 1 (reactive, informal practices) to Tier 4 (adaptive, predictive insights). Most healthcare organizations fall between Tiers 1 and 2 initially, which is a reasonable starting point.
Simultaneously, map your current security controls to both NIST subcategories and HIPAA requirements. This dual mapping not only supports compliance but also identifies potential vulnerabilities - particularly as Protected Health Information (PHI) flows through various systems, departments, and third-party vendors [8].
Step 2: Develop an Action Plan
Next, create a Target State Profile that outlines your organization's desired future cybersecurity state [7]. The gap between your current and target profiles will serve as the foundation for your improvement roadmap. Prioritize actions by evaluating risks based on their potential impact and likelihood, focusing resources on addressing the most critical vulnerabilities [7].
"The NIST Framework provides a common language for healthcare organizations to communicate about cybersecurity risk, enabling CISOs and compliance officers to align technical safeguards with business objectives." – Heights Consulting Group
Your action plan should include immediate technical improvements, such as implementing multi-factor authentication (MFA) across the organization or using network segmentation to isolate nonclinical systems (e.g., guest Wi-Fi or HVAC) from clinical networks. Adopting Zero Trust principles can further reduce your attack surface [8].
Set measurable milestones to track your progress on regulatory compliance and cybersecurity investments [4]. A cost-benefit analysis can help prioritize actions that deliver the greatest risk reduction. To simplify the planning process, NIST Quick Start Guides offer templates for creating Organizational Profiles and applying CSF Tiers [2].
Step 3: Monitor and Improve Continuously
Shift from reactive audits to proactive monitoring using AI-powered tools that detect anomalies and threats in real time [8]. Regular risk assessments and vulnerability scans are essential for identifying new weaknesses as your technology environment evolves [3]. Additionally, conducting tabletop exercises and incident response simulations can prepare your team and uncover procedural gaps [8].
The Govern function in NIST CSF 2.0 emphasizes the importance of leadership in cybersecurity oversight. Board members should review cyber risk metrics alongside financial and clinical quality measures during routine meetings to ensure cybersecurity remains a priority at the executive level [2][8].
Track your progress against Implementation Tiers and update your Target State Profile regularly [2]. Adopting the NIST CSF can lead to tangible benefits, such as reducing healthcare cyber insurance premiums by up to 66% and mitigating the financial impact of data breaches, which have cost the industry an average of $9.77 million annually for 14 consecutive years [8]. This aligns with research on the economic impact of third-party risk and the rising costs of healthcare data breaches. Up next, let’s explore how these measures benefit healthcare organizations.
Benefits of the NIST CSF for Healthcare Organizations
The NIST Cybersecurity Framework (CSF) offers healthcare organizations practical advantages, such as better insurance outcomes and a clear strategy for safeguarding patient data, medical devices, and clinical operations [1]. By shifting cybersecurity efforts from reactive to proactive, the framework not only strengthens operations but also builds trust with patients. Here's how it supports compliance, reduces risks, and enhances security practices.
Improving Compliance with Regulatory Standards
The NIST CSF helps translate HIPAA requirements into actionable steps. While HIPAA outlines the safeguards needed, the framework provides a hands-on guide to implementing administrative, physical, and technical controls [9].
"HIPAA laid the foundation, HITECH added accountability, and HITRUST and NIST provide the operational blueprint." – Nikhil Raj, Author, Ampcus Cyber
The HITECH Act requires organizations to prove their controls are not just documented but actively working. The NIST CSF supports this by providing tools for monitoring, documenting, and addressing issues, ensuring organizations meet these stricter enforcement standards [9]. It also allows healthcare providers to cross-map controls across frameworks, reducing duplicate work and aligning with the shift toward measurable, results-driven security compliance [9].
For providers working with Business Associates, the framework simplifies third-party risk assessments. Since HITECH expanded liability to include the entire ecosystem, using a common language to evaluate vendor security makes managing these responsibilities easier [9]. A well-implemented NIST CSF program can even bolster regulatory defensibility, potentially avoiding fines and legal complications.
Reducing Risks to Patient Safety and Data Security
The framework prioritizes patient safety by addressing security risks tied to connected medical devices and systems like Electronic Health Records (EHRs). Its six core functions guide organizations in managing assets, enforcing encryption, maintaining access controls, monitoring threats, and responding to incidents effectively [10].
Real-time threat detection tools, such as Security Information and Event Management (SIEM) systems, enable immediate breach identification, allowing faster mitigation [10]. This quick response reduces reliance on manual procedures during outages. Additionally, the framework's recovery protocols ensure systems are restored and data is retrieved swiftly after incidents like ransomware attacks [10].
Despite these advantages, only 44% of healthcare organizations currently meet NIST CSF standards, with approximately 37% lacking a cybersecurity contingency plan [1]. Tailoring the framework to specific healthcare needs and resources can improve IT security compliance and enhance the protection of Protected Health Information (PHI) [10].
"The framework provides a shared language and set of concepts that enable better communication both within security teams and toward the C-Suite." – Intraprise Health
Specialized platforms can further simplify the process, making it easier for organizations to align with the framework.
Using Censinet RiskOps™ for NIST CSF Alignment

Censinet RiskOps™ builds on the framework's structured approach by automating risk assessments and benchmarking for seamless CSF alignment. It streamlines third-party and enterprise risk evaluations, benchmarks cybersecurity practices against industry standards, and fosters collaboration across healthcare organizations and their vendors.
With its Censinet AI™ technology, the platform speeds up risk assessments by processing security questionnaires, summarizing evidence, and generating risk reports automatically. This blend of automation and human oversight helps organizations scale their risk management efforts while staying aligned with NIST CSF principles.
Censinet RiskOps™ acts as a centralized hub for managing risks associated with patient data, PHI, medical devices, and supply chains. Its AI-powered dashboard consolidates real-time data, directing critical findings to the appropriate stakeholders. This ensures continuous oversight across Governance, Risk, and Compliance (GRC) teams, helping healthcare organizations move from reactive compliance to a more proactive and adaptive security posture.
Conclusion
The NIST Cybersecurity Framework (CSF) serves as a strategic guide for achieving operational resilience in the healthcare sector. While HIPAA ensures legal compliance, the NIST CSF focuses on maintaining operations during cyber incidents - a crucial distinction in an era where healthcare data breaches cost an average of $9.77 million per incident[8].
"You need HIPAA to remain legal. You need NIST to remain operational." – CompassMSP
By leveraging its six core functions - Govern, Identify, Protect, Detect, Respond, and Recover - the CSF provides a full lifecycle approach to managing cyber risks. This framework not only addresses emerging threats like ransomware but also prioritizes clinical continuity. For organizations adopting the CSF, the benefits are tangible, with some reporting reductions in cyber insurance premiums by as much as 66%[1][8]. Despite these advantages, a significant gap persists, as only 44% of healthcare organizations currently meet these standards[1].
This gap between compliance and resilience has far-reaching consequences, affecting both operational costs and patient safety. However, the CSF’s scalability, through its Implementation Tiers, ensures that it can be adapted to the needs of organizations ranging from small clinics to expansive hospital systems.
Technology plays a pivotal role in closing this gap. Solutions like Censinet RiskOps™ simplify cybersecurity efforts by automating risk assessments, benchmarking against industry standards, and consolidating oversight of third-party and internal risks. Its AI-driven tools accelerate alignment with the NIST CSF while retaining the human judgment necessary for critical decisions. For healthcare organizations aiming to transition from reactive measures to proactive resilience, platforms like Censinet RiskOps™ provide a practical and effective way forward.
FAQs
How do I map HIPAA requirements to NIST CSF controls?
Healthcare organizations can align HIPAA requirements with NIST Cybersecurity Framework (CSF) by using crosswalk tools. These tools bridge the HIPAA Security Rule with NIST CSF's core categories: Identify, Protect, Detect, Respond, and Recover. This approach allows organizations to evaluate their security measures, pinpoint compliance gaps, and implement controls that satisfy both HIPAA and NIST standards efficiently.
What tier should my hospital or clinic aim for first?
Hospitals and clinics beginning their journey into cybersecurity should focus on the Partial or Risk-Informed tiers outlined in the NIST Cybersecurity Framework. The Partial tier is a starting point, reflecting minimal and often reactive security measures - perfect for organizations just getting started. Moving up to Risk-Informed means conducting initial risk assessments and implementing basic security practices. This creates a solid groundwork for improving defenses and meeting regulatory requirements, such as HIPAA. Taking it step by step allows for steady progress as resources and expertise expand.
How can we build a CSF profile without a big security team?
Creating a Cybersecurity Framework (CSF) profile doesn’t require a massive security team. By leveraging structured tools from NIST, such as the Organizational Profile template, you can map out your current and desired security states. Prioritize the five core functions: Identify, Protect, Detect, Respond, and Recover.
To make the process even smoother, platforms like Censinet RiskOps™ can help. These tools automate tasks like risk assessments and compliance tracking, making it easier to manage risks effectively - even with limited resources.
Related Blog Posts
- NIST CSF 2.0 Updates: What Healthcare Needs to Know
- NIST CSF vs IoT Device Risks in Healthcare
- NIST CSF Benchmark: Only 38% of Health Systems Report Full Implementation Across All Functions
- Healthcare’s Risk Paradox: Organizations Pass HIPAA Audits but Fail on Cyber Readiness Benchmarks
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"How do I map HIPAA requirements to NIST CSF controls?","acceptedAnswer":{"@type":"Answer","text":"<p>Healthcare organizations can align <strong>HIPAA requirements</strong> with <strong>NIST Cybersecurity Framework (CSF)</strong> by using crosswalk tools. These tools bridge the <strong>HIPAA Security Rule</strong> with NIST CSF's core categories: <strong>Identify, Protect, Detect, Respond, and Recover</strong>. This approach allows organizations to evaluate their security measures, pinpoint compliance gaps, and implement controls that satisfy both HIPAA and NIST standards efficiently.</p>"}},{"@type":"Question","name":"What tier should my hospital or clinic aim for first?","acceptedAnswer":{"@type":"Answer","text":"<p>Hospitals and clinics beginning their journey into cybersecurity should focus on the <strong>Partial</strong> or <strong>Risk-Informed</strong> tiers outlined in the NIST Cybersecurity Framework. The <strong>Partial</strong> tier is a starting point, reflecting minimal and often reactive security measures - perfect for organizations just getting started. Moving up to <strong>Risk-Informed</strong> means conducting initial risk assessments and implementing basic security practices. This creates a solid groundwork for improving defenses and meeting regulatory requirements, such as HIPAA. Taking it step by step allows for steady progress as resources and expertise expand.</p>"}},{"@type":"Question","name":"How can we build a CSF profile without a big security team?","acceptedAnswer":{"@type":"Answer","text":"<p>Creating a Cybersecurity Framework (CSF) profile doesn’t require a massive security team. By leveraging structured tools from NIST, such as the <strong>Organizational Profile template</strong>, you can map out your current and desired security states. Prioritize the five core functions: <strong>Identify</strong>, <strong>Protect</strong>, <strong>Detect</strong>, <strong>Respond</strong>, and <strong>Recover</strong>.</p> <p>To make the process even smoother, platforms like <strong>Censinet RiskOps™</strong> can help. These tools automate tasks like risk assessments and compliance tracking, making it easier to manage risks effectively - even with limited resources.</p>"}}]}
Key Points:
What is the NIST Cybersecurity Framework and why has it become the primary security standard for healthcare organizations?
- The NIST CSF is a set of voluntary guidelines, standards, and practices developed by the National Institute of Standards and Technology to help organizations manage and reduce cybersecurity risks, designed to be adaptable across industries, organizational sizes, and varying levels of cybersecurity maturity
- Within one year of its 2014 launch, 30% of US organizations were already using the framework, and by 2017, 95% of advanced healthcare organizations with dedicated security teams had implemented it, reflecting the framework's practical utility across the healthcare sector
- The average cost of a healthcare data breach has been $9.77 million annually for 14 consecutive years, and 78% of healthcare organizations reported cybersecurity incidents in a single year, establishing the scale of the threat that NIST CSF adoption is designed to address
- The framework bridges the gap between HIPAA's regulatory requirements and actionable security practices by not only defining what needs protection but providing structured guidance on how to implement administrative, physical, and technical safeguards that meet HIPAA standards
- A shared cybersecurity vocabulary is one of the framework's most practical benefits for healthcare, enabling consistent communication between technical teams and non-technical executives about current security measures, future goals, improvement areas, and risk levels without requiring security expertise to interpret
- Healthcare organizations using the NIST CSF report up to 66% smaller increases in cyber insurance premiums compared to non-adopters, demonstrating that the framework's risk reduction benefits translate directly into measurable financial outcomes beyond regulatory compliance
What are the six core functions of NIST CSF 2.0 and how does each apply to healthcare-specific security challenges?
- Govern, introduced in CSF 2.0, establishes the organization's cybersecurity strategy, policies, and risk management framework, and for healthcare this means embedding cybersecurity into everyday operations by developing policies for PHI management and medical device procurement that align security with the organization's patient care mission
- Identify emphasizes understanding risks to critical assets including PHI, connected medical devices and IoT systems, and supply chains, requiring healthcare organizations to catalog all medical devices and evaluate third-party vendor risks to map potential vulnerabilities across the full care delivery ecosystem
- Protect ensures safeguards are implemented and functioning, covering data encryption at rest and in transit, multi-factor authentication for system access, and access controls that limit PHI exposure to authorized clinical and administrative personnel based on role
- Detect involves continuous monitoring for threats and anomalies, with healthcare organizations deploying intrusion detection systems to identify unauthorized access to EHR systems, detect data exfiltration attempts, and surface indicators of compromise before incidents escalate into reportable breaches
- Respond outlines structured steps to mitigate incident impact, and with the average cost of a healthcare ransomware attack reaching $3.2 million, having a detailed and tested response plan that minimizes service disruptions and maintains clinical operations during incidents is a direct patient safety investment
- Recover focuses on restoring systems and operations after an incident, which in healthcare specifically means recovering patient data from secure, tested backups to ensure continuity of care and minimize the gap between incident containment and the resumption of clinical services
How do NIST CSF Implementation Tiers work and how should healthcare organizations use them to guide maturity progression?
- Tier 1 (Partial) describes organizations where risk management is informal and reactive with limited awareness of supply chain risks, Tier 2 (Risk Informed) where management recognizes risks and some processes address external threats, Tier 3 (Repeatable) where policies are formally approved and responses are consistent, and Tier 4 (Adaptive) where practices evolve based on lessons learned and predictive insights
- Most healthcare organizations fall between Tiers 1 and 2 initially, which is a recognized and acceptable starting point, with the framework explicitly noting that tiers should complement rather than replace an organization's existing risk management methodology
- Not every organization needs to target Tier 4, and NIST advises that progression to higher tiers is appropriate when risks or regulatory mandates require it or when a cost-benefit analysis demonstrates that the investment will effectively protect critical assets such as EHR systems relative to the cost
- Starting by assessing Tier levels for a few critical systems such as patient databases or EHR access controls prevents overwhelming implementation and builds the momentum and organizational experience needed for broader adoption across all systems and departments
- Defining a desired Tier for each category based on risk tolerance and operational goals allows healthcare organizations to create differentiated maturity targets that focus the highest investment on the highest-risk systems rather than applying uniform tier targets across all functions
- Tier progression should be tracked against Implementation Tiers regularly with Target State Profile updates reflecting actual progress, because static targets quickly become irrelevant as the threat landscape, regulatory environment, and technology footprint of healthcare organizations evolve
How should healthcare organizations create and use NIST CSF Organizational Profiles?
- Profiles make the CSF Core actionable by tailoring it to an organization's specific risk environment, budget, and operational context, allowing healthcare providers to prioritize the functions, categories, and subcategories most relevant to their particular patient population, technology landscape, and regulatory obligations
- A Current State Profile documents existing security measures across all six functions, providing the factual baseline from which gap analysis and improvement planning can proceed rather than building security programs from assumptions about existing capabilities
- A Target State Profile reflects the desired future security posture shaped by regulatory requirements, business objectives, and acceptable risk levels, with the gap between current and target profiles serving as the direct input for prioritizing improvement actions
- Gap analysis prioritizes actions by evaluating risks based on potential impact and likelihood, focusing resources on the most critical vulnerabilities first rather than attempting comprehensive simultaneous improvement across all profile gaps
- For organizations already conducting HIPAA risk analyses, adding a column showing how NIST functions address identified risks simplifies both the profile creation process and subsequent compliance audits by creating a unified documentation framework that satisfies both sets of requirements simultaneously
- Profiles serve as a communication tool for CISOs presenting to boards and executives, providing a structured way to explain how specific security investments protect critical outcomes including patient safety and operational stability without requiring technical expertise to interpret
What are the three steps for applying the NIST CSF to a healthcare security program?
- Step 1 assesses the current cybersecurity state by creating a Current State Profile documenting existing controls across all six functions, mapping those controls to both NIST subcategories and HIPAA requirements, and evaluating maturity using Implementation Tiers to establish a documented baseline that makes gaps visible and measurable
- Asset mapping is a foundational requirement of Step 1 because organizations cannot protect what they do not know they have, making the cataloging of medical devices, PHI systems, third-party vendor connections, and clinical application integrations a prerequisite for meaningful risk assessment
- Step 2 develops an action plan by creating a Target State Profile, comparing it to the current state to identify the gap, and prioritizing actions based on risk impact and likelihood with measurable milestones that allow progress to be tracked against both regulatory compliance and security investment goals
- Immediate technical improvements in the action plan should include MFA implementation, network segmentation isolating non-clinical systems from clinical networks, and Zero Trust principles that reduce the attack surface available to both external attackers and compromised credentials
- Step 3 shifts from reactive audits to continuous improvement using AI-powered monitoring tools that detect anomalies in real time, regular risk assessments and vulnerability scans identifying new weaknesses as the technology environment evolves, and tabletop exercises testing response capabilities and surfacing procedural gaps
- The Govern function in CSF 2.0 requires board-level cybersecurity oversight, with cyber risk metrics reviewed alongside financial and clinical quality measures at regular board meetings, ensuring that security remains a leadership priority rather than solely an IT operational concern
What measurable benefits do healthcare organizations gain from NIST CSF adoption?
- Healthcare organizations adopting the NIST CSF report up to 66% smaller increases in cyber insurance premiums compared to non-adopters, with the 2024 study of 58 healthcare organizations finding CSF adopters experienced a 6% premium increase versus an 18% increase for non-adopters
- The framework improves regulatory compliance efficiency by enabling cross-mapping of controls across HIPAA, HITECH, NIST, and HITRUST simultaneously, reducing duplicate assessment work and creating a single set of documented controls that satisfies multiple regulatory requirements
- HITECH requires organizations to prove controls are not only documented but actively working, and the NIST CSF supports this by providing monitoring, documentation, and issue-tracking tools that demonstrate operational effectiveness rather than just policy existence
- Only 44% of healthcare organizations currently meet NIST CSF standards despite 14 consecutive years of leading breach costs at $9.77 million per incident, indicating the gap between framework availability and implementation that represents the sector's most significant cybersecurity risk reduction opportunity
- The CSF's scalability through Implementation Tiers ensures it can be adapted from small clinics with limited security staff to expansive hospital systems with dedicated GRC teams pursuing comprehensive cross-framework alignment
- Platforms such as Censinet RiskOps automate risk assessments, benchmark against industry standards, and consolidate oversight of third-party and internal risks while using AI-driven tools to accelerate NIST CSF alignment, enabling healthcare organizations to transition from reactive compliance to proactive and adaptive security posture


