Ultimate Guide to Cloud Vendor Risk Management
Post Summary
Cloud vendors supporting EHR systems, medical imaging, telehealth platforms, and data backup operate within healthcare's 24/7 care delivery environment, meaning vendor breaches, outages, or ransomware attacks directly disrupt patient care operations, compromise protected health information, and create HIPAA compliance exposure that can result in regulatory penalties.
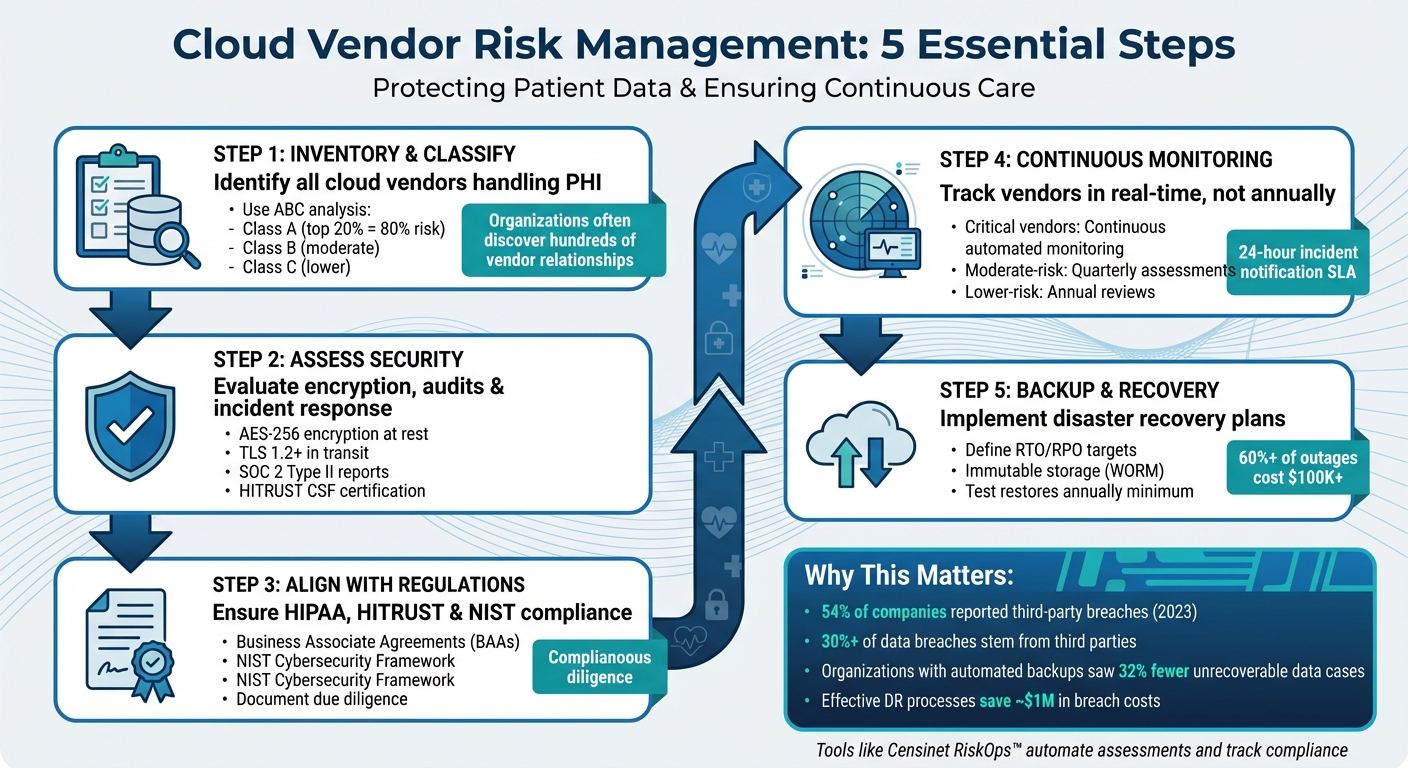
Healthcare organizations should use ABC analysis based on the Pareto Principle, classifying the top 20% of vendors representing 80% of risk as Class A requiring the most intensive oversight, Class B vendors representing moderate risk, and Class C vendors with lower risk levels, with classification based on system access, data types handled, integration points, and overall business importance.
A healthcare cloud vendor risk assessment must evaluate encryption standards including AES-256 for data at rest and TLS 1.2 or higher for data in transit, Business Associate Agreement completeness and healthcare-specific protections, third-party audit reports such as SOC 2 Type II and HITRUST CSF certification, and incident response capabilities including breach notification timelines and forensic investigation practices.
Critical vendors require continuous automated monitoring integrated with SIEM systems and frequent security ratings, moderate-risk vendors benefit from quarterly automated assessments combined with continuous security ratings, and lower-risk vendors can be managed with annual questionnaires supported by automated external ratings, with all vendors contractually required to support monitoring efforts and provide 24-hour breach notification.
HIPAA-compliant cloud backup solutions must include encryption in transit and at rest, role-based access controls and multi-factor authentication for administration, immutable write-once read-many storage, automated policy-based scheduling, comprehensive audit logs, geographic redundancy with SOC 2 Type II certification, and documented Recovery Time Objectives and Recovery Point Objectives for each critical system.
Key metrics include mean time to detect and mean time to respond to vendor-related incidents, percentage of high-risk vendors under active monitoring, number of vendor-related alerts investigated monthly, percentage of critical vendors integrated with SIEM systems, and zero repeat critical findings from the same vendor across two consecutive quarters.
Healthcare organizations depend on cloud vendors for critical services like EHRs, medical imaging, and telehealth platforms. But when a vendor faces a breach or outage, the consequences can disrupt patient care, compromise safety, and lead to regulatory penalties. Managing these risks starts with identifying and addressing vulnerabilities in vendor systems.
Here’s what you need to know:
Tools like Censinet RiskOps™ can simplify the process by automating risk assessments and tracking vendor compliance. Start by focusing on high-risk vendors, embedding security into procurement, and building a structured framework to safeguard operations and patient care.
5-Step Healthcare Cloud Vendor Risk Management Framework
Cloud Cybersecurity: Strategies for Managing Vendor Risk (Webinar)
sbb-itb-535baee
Building a Vendor Risk Management Framework
Start by creating a comprehensive list of all vendors and their access to your systems. Healthcare organizations often underestimate the number of vendor relationships they maintain - sometimes discovering hundreds of cloud services interacting with protected health information (PHI) across various departments. Without a complete inventory, it becomes difficult to assess risks effectively or respond to incidents.
Creating a Vendor Inventory and Classification System
First, identify every cloud vendor that handles PHI. This includes not only well-known partners like EHR providers and medical imaging platforms but also less obvious tools, such as cloud-based scheduling systems, patient communication apps, and analytics platforms. Centralize this information into a system that provides real-time visibility across departments. Cloud-based inventory management tools can integrate with existing hospital systems (e.g., ERP or EHR platforms), allowing administrative and clinical teams to maintain coordinated oversight. This centralized inventory is the foundation for effective risk classification.
To prioritize resources, classify vendors using ABC analysis:
This method, based on the Pareto Principle, ensures you focus on the relationships that carry the greatest potential impact.
For each vendor, document details such as system access, data types handled, integration points, and overall business importance. Update this inventory continuously rather than annually. Automated tools can help track changes, flagging critical events like upcoming contract renewals, expiring security certifications, or new integrations. Research suggests that implementing inventory control measures in large hospital systems can reduce costs by up to 20%[6]. In vendor risk management, focusing on high-risk relationships can deliver similar efficiencies.
Core Elements of a Vendor Risk Assessment Framework
An effective vendor risk assessment framework evaluates vendors across several key areas.
Start with encryption standards. Confirm that vendors use robust encryption protocols, such as AES-256 for data at rest and TLS 1.2 (or higher) for data in transit. Additionally, ensure encryption key management meets industry standards and, when possible, that your organization retains control over the keys.
Business Associate Agreements (BAAs) are critical under HIPAA for any vendor handling PHI. These agreements should clearly outline responsibilities for protecting PHI, breach notification timelines, and audit rights. Generic templates may not include healthcare-specific protections, so it’s essential to review BAAs carefully. Key elements to include are incident response timeframes, data deletion protocols upon contract termination, and the organization’s right to conduct security audits.
Third-party audits provide independent verification of a vendor’s security practices. For example:
Request up-to-date audit reports during vendor evaluations; reports older than 12 months may not reflect the vendor’s current security posture.
Assess incident response capabilities by asking vendors specific questions, such as:
Also, review documentation of past incidents and their resolutions. Vendors that are transparent about previous security events and show a commitment to improvement are generally more dependable.
Platforms like Censinet RiskOps™ can simplify this process by offering standardized healthcare-specific questionnaires, automated workflows for tracking vendor responses, and a centralized repository for BAAs, audit reports, and other security documentation. This eliminates the spreadsheet chaos often associated with risk management and ensures consistent evaluations across all vendors.
Aligning Risk Management with Regulatory Requirements
Your framework must align with regulatory standards to meet compliance requirements. The NIST Cybersecurity Framework provides a flexible structure built around five core functions: Identify, Protect, Detect, Respond, and Recover. For instance, maintaining a vendor inventory aligns with the “Identify” function, while incident response planning falls under “Respond.”
For a more prescriptive approach, the HITRUST CSF consolidates requirements from HIPAA, HITECH, PCI DSS, and other regulations into a single framework with multiple control categories and maturity levels. Many healthcare organizations require their highest-risk vendors (Class A) to maintain HITRUST certification as a baseline requirement.
It’s also crucial to document how your vendor risk management program addresses specific HIPAA requirements. This includes:
Maintaining records of due diligence - such as assessment questionnaires, audit reports, and remediation plans - can demonstrate compliance during regulatory audits. Regular internal reviews help ensure that your framework remains effective and that established protocols are consistently applied across all departments.
Continuous Monitoring and Incident Response
Creating a framework is just the starting point. Vendor risk isn't static - cloud environments change, new vulnerabilities arise, and vendors can face breaches. To stay ahead, continuous monitoring and a well-prepared incident response plan are essential. These practices help detect problems early, preventing them from escalating into breaches or disruptions that could jeopardize patient care and HIPAA compliance.
Setting Up Continuous Monitoring Systems
Continuous monitoring moves vendor risk management away from static, annual questionnaires to real-time oversight. The aim is to spot vendor-originated threats early, ensure ongoing compliance with HIPAA and other healthcare requirements, and safeguard critical clinical and business services [3][5].
Vendors can be categorized by risk level:
SIEM systems are at the heart of technical monitoring. By integrating vendor audit logs, API events, and identity activities into your SIEM, you can correlate activity and set alerts for high-risk signals - like unusual logins, spikes in PHI access, or abnormal data transfers [3][7].
To strengthen monitoring, pair SIEM data with cloud security posture management (CSPM) and cloud workload protection platforms (CWPP). These tools track configuration changes and access shifts across vendor environments, aligning them with frameworks like NIST SP 800-53 or CIS Benchmarks [3][7]. External security ratings services add another layer by scanning vendors' public-facing systems for vulnerabilities, exposed credentials, or malware.
Healthcare-focused platforms like Censinet RiskOps™ simplify continuous monitoring by unifying vendor questionnaires, compliance tracking, and risk findings. Real-time dashboards can show which vendors are up-to-date on certifications, highlight unresolved risks, and flag vendors with elevated risk levels.
Incorporate monitoring requirements into vendor contracts. Specify that vendors must support continuous monitoring efforts, provide evidence when requested, and allow periodic security assessments. Include incident notification SLAs, mandating notification within 24 hours of any breach or security event impacting patient data [2][8][1].
To measure your monitoring program's success, track metrics like mean time to detect (MTTD) and mean time to respond (MTTR) to incidents, the percentage of high-risk vendors under active monitoring, and the number of vendor-related alerts investigated monthly. A mature program might aim for goals like "100% of critical vendors integrated with SIEM", "all anomalies triaged within four hours", or "zero repeat critical findings from the same vendor across two quarters" [3].
Even with robust monitoring, a fast and effective incident response plan is key to minimizing damage.
Creating a Vendor Incident Response Plan
Despite the best monitoring tools, vendor incidents can still happen. A clear incident response plan ensures your team knows exactly how to act if a vendor experiences a breach, ransomware attack, or service disruption.
Start by defining what qualifies as a vendor "security incident" or "breach" under HIPAA. Examples include unauthorized access, data exfiltration, ransomware attacks, or misconfigured storage that exposes patient records. Clearly outline roles and responsibilities: decide who at the vendor must notify your organization, who leads forensic investigations, who handles containment actions (like disabling accounts or revoking API keys), and who manages legal, regulatory, and patient communications.
Notification timelines are critical. HIPAA allows up to 60 days for breach notifications, but vendors should be required to notify you within 24 hours of discovering an issue. Early notification enables your team to start containment and investigation immediately [2][8][1].
Develop playbooks for common scenarios, such as suspending access, isolating affected systems, gathering forensic logs, and coordinating responses with legal and clinical teams. Specific playbooks should address issues like misconfigured cloud storage, vendor ransomware attacks, and supply chain compromises.
Set clear escalation criteria to determine when your enterprise incident response team should be activated. Triggers might include confirmed PHI exposure, incidents impacting clinical systems, or regulatory reporting requirements. Pre-assign roles across security, privacy, legal, compliance, IT, and clinical leadership to ensure everyone knows their responsibilities.
After an incident, follow a structured recovery process: apply patches, harden configurations, rotate credentials, restore from verified backups, and validate data integrity. Test restored systems with clinical and business teams. Conduct a "lessons learned" review within 30 days to update vendor risk scores, refine monitoring rules, and adjust playbooks. If necessary, re-evaluate or replace the vendor [3].
Routine testing is essential. Run tabletop exercises at least once a year to simulate scenarios like a major cloud vendor outage or PHI breach. This ensures communication paths, decision-making processes, and technical playbooks are ready for real incidents [8][1].
Include incident response requirements in your Business Associate Agreements (BAAs) and service contracts. Specify SLAs for evidence sharing, forensic cooperation, and post-incident reporting. Ensure the contract allows you to participate in or receive detailed information from the vendor's investigations and reviews. This contractual clarity ensures vendors understand their responsibilities and provides leverage if they fall short [2][8][1].
Regular testing and post-incident reviews strengthen both monitoring and response processes, helping you maintain a strong vendor risk management strategy.
Cloud Backup and Disaster Recovery Best Practices
Cloud backup and disaster recovery play a crucial role in managing vendor risks. When a cloud vendor faces an outage, ransomware attack, or data corruption, the ability to swiftly restore patient data is what ensures uninterrupted care. Under HIPAA, maintaining the availability of electronic protected health information (ePHI) is just as critical as safeguarding its confidentiality. A failure in backup systems can lead to compliance violations.
The financial risks are substantial. According to the Uptime Institute's 2022 report, over 60% of major outages cost more than $100,000. Studies from the Ponemon Institute and IBM reveal that organizations with effective backup and disaster recovery processes can save about $1 million in average breach costs. However, a 2023 Sophos survey of 3,000 IT professionals highlights a troubling reality: while 94% of ransomware victims tried to restore data from backups, only 57% managed to recover even half of their information. This underscores the gap between simply having backups and ensuring they are functional and reliable - something every vendor risk management strategy must address.
Required Features for HIPAA-Compliant Cloud Backup Solutions
Cloud backup vendors must sign a Business Associate Agreement (BAA), but that’s just the start. To meet HIPAA Security Rule requirements and address modern threats like ransomware, backup solutions should include these critical features:
Organizations should also define and document Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO) for each critical system. For instance, a Tier 0 clinical system, like an electronic health record (EHR), might require an RTO of four hours and an RPO of 15 minutes. These targets should be part of vendor contracts and supported by backup systems with features like multi-region replication. According to an IDC survey, companies with automated, policy-driven backups and regular testing saw 32% fewer cases of unrecoverable data.
Connecting Backup Solutions to Vendor Risk Management
Once you’ve identified the essential backup features, integrate them into your broader vendor risk framework. Evaluate vendors’ backup architectures, RTO/RPO targets, data export processes, and restore testing results. Include specific backup and disaster recovery requirements in your BAAs and service contracts, such as encryption standards, RBAC/MFA policies, immutable storage capabilities, and minimum RTO/RPO benchmarks. Vendors should also provide clear data export and portability procedures to ensure you can restore data independently in case of vendor failure or contract termination.
NIST emphasizes that contract terms and service level agreements (SLAs) are critical for cloud security authorization. These agreements should clearly address backup protocols, data portability, and timely data return if services are terminated [9]. Require vendors to conduct regular restore tests - at least annually for all critical systems, and more frequently for Tier 0 and Tier 1 clinical systems - and include these test results in vendor risk assessments. Tabletop exercises simulating vendor outages or ransomware attacks can also help test communication workflows, escalation points, and shared responsibilities outlined in your incident response plan.
Aligning vendor backup and disaster recovery processes with your internal incident response strategies ensures your team knows which backups to use, who to contact, and how to validate restored data during an incident. This coordination reduces downtime and protects patient care.
Tools like Censinet RiskOps™ simplify third-party risk assessments by tracking vendor backup and disaster recovery controls, remediation efforts, and test outcomes across your cloud vendor portfolio. This centralized approach helps you compare vendors against industry benchmarks and address any gaps in backup or disaster recovery systems.
The HHS "Cybersecurity Best Practices for the Health Sector" highlights the importance of regular, tested backups - whether stored offline or as immutable copies - as a safeguard against ransomware and other disruptions. Incorporating tested backup solutions into your vendor risk framework ensures that care delivery continues even during vendor-related disruptions.
Step-by-Step Guide to Implementing Vendor Risk Management
Implementing vendor risk management involves a structured, phased approach. Instead of trying to evaluate every vendor at once, start with those handling your most sensitive data or supporting critical operations. This method allows your team to gain experience, refine processes, and show results before scaling up.
Phased Implementation Approach
Begin by focusing on Tier 0 and Tier 1 vendors, such as your EHR provider, backup vendor, or medical device manufacturers. Once these higher-risk vendors are addressed, you can gradually include lower-risk ones. It's also crucial to embed vendor risk management into your procurement process from the start. Require security questionnaires, certification reviews, and BAAs before signing contracts. This proactive step helps prevent unnecessary risks and ensures vendors meet your security standards before gaining access to your systems. Considering that 54% of companies reported breaches caused by third parties in 2023, and over 30% of data breaches stem from third-party incidents, integrating risk management into procurement is a necessity [10].
Using Technology to Manage Risk
Managing vendor risk manually becomes impractical as your vendor list grows. Tracking assessments, remediation, and reassessments through spreadsheets and email chains is inefficient and error-prone. Technology platforms tailored for healthcare risk management can automate repetitive tasks and provide centralized oversight of your vendor ecosystem.
Censinet RiskOps™ offers tools to simplify third-party risk assessments. It automates tasks like distributing questionnaires, tracking responses, and flagging high-risk findings for immediate review. Its Censinet AI™ feature allows vendors to complete security questionnaires in seconds while summarizing their evidence and documentation. This automation speeds up the process without sacrificing the human oversight necessary for critical decisions.
Centralized platforms also enhance collaboration across departments. Around 30% of organizations lack dedicated vendor risk assessment staff, making it essential to leverage resources from IT, legal, compliance, procurement, and operations [12]. Automated tools with features like document sharing and real-time alerts ensure that relevant findings are routed to the right stakeholders. For instance, if a vendor's SOC 2 report highlights a control issue, the platform can notify IT security for review and legal for potential contract amendments. These tools complement continuous monitoring efforts, ensuring technical and procedural measures work hand in hand.
Training Staff and Engaging Stakeholders
Successful vendor risk management depends on well-trained staff and active collaboration among stakeholders. A cross-departmental approach ensures thorough assessments and effective monitoring. Key departments involved include IT, finance, operations, procurement, legal, and compliance [14,17]. Form a risk assessment team with clearly defined roles to maintain accountability and consistency during evaluations and incidents [17,18].
Create role-specific documentation to guide staff. For example, senior management and board members need high-level policies explaining objectives, governance, and key risk indicators. Meanwhile, front-line staff require detailed procedures for tasks like onboarding vendors, escalating security issues, or documenting assessments [11].
Develop a strong reporting process to keep senior leadership informed about vendor risks. This is often a regulatory requirement [15,18]. Regular reports should cover new high-risk vendors, remediation updates, and emerging threats. Conduct internal audits to identify gaps or errors before external reviews, and use feedback from departments like legal and logistics to enhance vendor compliance [15,16,18].
Conclusion
Managing cloud vendor risks is a continuous process that safeguards patient safety, ensures compliance with regulations, and keeps healthcare operations running smoothly. With cloud vendors playing a critical role in areas like EHR systems and data backups, any lapse in vendor security can disrupt operations and put sensitive patient data at risk. This makes vendor oversight an absolute priority for healthcare organizations.
To build a strong vendor risk management program, focus on key steps: classify vendors by risk level, perform detailed risk assessments, maintain ongoing monitoring, and ensure that backup solutions comply with HIPAA standards. These actions create a solid foundation for a program that evolves alongside your vendor network and the changing threat landscape.
However, technical measures alone aren’t enough - they need strong leadership to succeed. Executive and clinical leaders are essential in driving this effort. Vendor risk management depends on collaboration across departments, clear governance structures, and sufficient resources. Leaders must advocate for the program, allocate budgets for necessary tools and training, and ensure vendors adhere to their security commitments. Without this backing, even the most well-designed framework may fall short.
With leadership support, leveraging specialized tools can significantly enhance your program's effectiveness. Platforms like Censinet RiskOps™ simplify third-party risk assessments, automate repetitive tasks, and centralize vendor risk management. These tools help healthcare organizations move beyond manual processes, enabling scalable and efficient programs that meet regulatory and operational demands.
Take proactive steps in the next 90 days to strengthen your vendor risk management strategy. Start by cataloging your Tier 0 and Tier 1 vendors, conducting initial risk assessments, and embedding vendor security requirements into your procurement workflows. Achieving quick wins with high-priority vendors sets the stage for expanding your program to include lower-risk vendors. The effort you invest now will help protect patient care, ensure compliance, and secure your organization’s operational future.
FAQs
How do I determine which cloud vendors are 'Tier 0' or 'critical'?
To pinpoint 'Tier 0' or critical cloud vendors, start by identifying those responsible for managing your most sensitive assets. This includes systems tied to identity management, administrative accounts, or core infrastructure. These vendors typically have access to vital control planes or environments with elevated privileges. Carefully assess their role in handling sensitive data and systems, and implement a tiered access governance model. This approach ensures access is limited to trusted personnel, safeguarding these critical assets effectively.
What should a HIPAA Business Associate Agreement (BAA) include for cloud vendors?
A HIPAA Business Associate Agreement (BAA) for cloud vendors is a critical document that specifies how Protected Health Information (PHI) is handled. It should clearly define the permitted uses and disclosures of PHI, ensuring adherence to HIPAA regulations. To strengthen security, safeguards like encryption and multi-factor authentication should be mandatory.
The agreement must also cover essential details, such as breach notification timelines, the vendor's responsibilities, and the requirement for subcontractors to comply with HIPAA standards. Regular audits and updates are crucial to address new risks and changing regulations, ensuring both accountability and the protection of sensitive information.
What metrics best demonstrate that my vendor monitoring and incident response are effective?
Key performance indicators (KPIs) like mean time to risk resolution, vendor risk ratings, and compliance completion rates play a crucial role in evaluating performance. These metrics help gauge how efficiently risks are addressed, monitor vendor risk levels, and track adherence to security and regulatory requirements. Combined, they offer valuable insights into the effectiveness of vendor monitoring and incident response - especially vital in industries like healthcare, where compliance and safety are top priorities.
Related Blog Posts
- Healthcare Vendor Breach Response: Best Practices
- HIPAA Compliance for Cloud Services: Checklist
- The AWS Outage Exposed Cloud Vulnerabilities - What It Means for Healthcare Business Continuity
- Cloud Vendor Risk Management for Healthcare: Security, Compliance, and Continuity
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"How do I determine which cloud vendors are 'Tier 0' or 'critical'?","acceptedAnswer":{"@type":"Answer","text":"<p>To pinpoint 'Tier 0' or critical cloud vendors, start by identifying those responsible for managing your most sensitive assets. This includes systems tied to identity management, administrative accounts, or core infrastructure. These vendors typically have access to vital control planes or environments with elevated privileges. Carefully assess their role in handling sensitive data and systems, and implement a tiered access governance model. This approach ensures access is limited to trusted personnel, safeguarding these critical assets effectively.</p>"}},{"@type":"Question","name":"What should a HIPAA Business Associate Agreement (BAA) include for cloud vendors?","acceptedAnswer":{"@type":"Answer","text":"<p>A HIPAA Business Associate Agreement (BAA) for cloud vendors is a critical document that specifies how <strong>Protected Health Information (PHI)</strong> is handled. It should clearly define the permitted uses and disclosures of PHI, ensuring adherence to HIPAA regulations. To strengthen security, safeguards like <strong>encryption</strong> and <strong>multi-factor authentication</strong> should be mandatory.</p> <p>The agreement must also cover essential details, such as <strong>breach notification timelines</strong>, the vendor's responsibilities, and the requirement for subcontractors to comply with HIPAA standards. Regular audits and updates are crucial to address new risks and changing regulations, ensuring both accountability and the protection of sensitive information.</p>"}},{"@type":"Question","name":"What metrics best demonstrate that my vendor monitoring and incident response are effective?","acceptedAnswer":{"@type":"Answer","text":"<p>Key performance indicators (<strong>KPIs</strong>) like <strong>mean time to risk resolution</strong>, <strong>vendor risk ratings</strong>, and <strong>compliance completion rates</strong> play a crucial role in evaluating performance. These metrics help gauge how efficiently risks are addressed, monitor vendor risk levels, and track adherence to security and regulatory requirements. Combined, they offer valuable insights into the effectiveness of vendor monitoring and incident response - especially vital in industries like healthcare, where compliance and safety are top priorities.</p>"}}]}
Key Points:
Why is cloud vendor risk management critical for healthcare organizations and what is the scope of the challenge?
- Cloud vendors are now embedded in every critical healthcare operation, from EHR systems and medical imaging platforms to telehealth services, patient communication tools, analytics platforms, and cloud-based scheduling systems that interact with protected health information across clinical and administrative departments
- Healthcare organizations frequently underestimate the number of vendor relationships they maintain, often discovering hundreds of cloud services interacting with PHI across departments when they conduct their first comprehensive inventory, many of which have never been formally assessed
- 54% of companies reported breaches caused by third parties in 2023 and over 30% of data breaches stem from third-party incidents, making vendor risk management a primary rather than secondary security concern for healthcare organizations
- The February 2024 Change Healthcare breach demonstrated the systemic consequences of inadequate cloud vendor risk management, disrupting 15 billion annual transactions, causing financial strain for 94% of hospitals, and affecting 74% of organizations' ability to deliver patient care
- HIPAA holds covered entities accountable for the security practices of their business associates through Business Associate Agreement requirements, meaning that a vendor's security failure becomes a regulatory compliance event for the healthcare organization regardless of internal security posture
- Healthcare's 24/7 operational model means vendor outages or breaches have no scheduled maintenance window to limit impact, making risk management investment directly proportional to the organization's ability to sustain continuous patient care delivery
How should healthcare organizations build a vendor inventory and classification system for cloud vendor risk management?
- A comprehensive vendor inventory must include every cloud service interacting with PHI, not only well-known EHR and imaging partners but also cloud-based scheduling systems, patient communication apps, analytics platforms, and any other tool with access to protected health information
- ABC analysis based on the Pareto Principle provides the most practical classification methodology, identifying the top 20% of vendors representing 80% of risk as Class A requiring intensive oversight, with Class B and Class C vendors receiving proportionally less frequent assessment and monitoring
- Each vendor record should document system access levels, data types handled, integration points, and overall business importance to support risk scoring and ensure that classification decisions are based on documented evidence rather than subjective judgment
- Inventory should be updated continuously rather than annually, with automated tools tracking critical events including upcoming contract renewals, expiring security certifications, and new integrations that could change a vendor's risk profile between scheduled review cycles
- Centralizing the inventory into a system providing real-time visibility across departments enables clinical and administrative teams to maintain coordinated oversight rather than managing vendor relationships in departmental silos that obscure the organization's total vendor risk exposure
- Research suggests that inventory control measures in large hospital systems can reduce costs by up to 20%, and the same efficiency principle applies to vendor risk management where focusing resources on Class A relationships delivers the greatest risk reduction per assessment dollar
What are the core elements of an effective healthcare cloud vendor risk assessment framework?
- Encryption standard verification is the technical foundation of any vendor assessment, requiring confirmation of AES-256 for data at rest and TLS 1.2 or higher for data in transit, with assessment of encryption key management practices and, where possible, verification that the healthcare organization retains control over encryption keys
- Business Associate Agreements must be reviewed for healthcare-specific protections beyond generic templates, including incident response timeframes, data deletion protocols upon contract termination, the organization's right to conduct security audits, and breach notification timelines that require vendor notification within 24 hours rather than relying on HIPAA's 60-day maximum
- Third-party audit reports provide independent verification of vendor security practices, with SOC 2 Type II reports covering a 12-month period and HITRUST CSF certification demonstrating compliance with HIPAA, HITECH, and NIST standards simultaneously — reports older than 12 months should not be accepted as they may not reflect current security posture
- Incident response capability assessment should ask specific operational questions including average response time to security incidents, customer breach notification processes, forensic investigation tools used, and documentation of past incidents and their resolutions, with transparency about previous security events being a positive indicator of vendor reliability
- NIST CSF alignment and HITRUST certification requirements should be embedded in vendor classification standards, with Class A vendors typically required to maintain HITRUST CSF certification as a baseline, ensuring that the highest-risk vendor relationships meet the most rigorous independent verification standards
- Automated risk management platforms such as Censinet RiskOps simplify vendor assessment by providing standardized healthcare-specific questionnaires, automated workflows for tracking vendor responses, and a centralized repository for BAAs, audit reports, and security documentation that eliminates the spreadsheet-based management that creates compliance gaps
How should healthcare organizations structure continuous monitoring and incident response for cloud vendors?
- Continuous monitoring shifts vendor risk management from static annual questionnaires to real-time oversight, aiming to detect vendor-originated threats early, ensure ongoing HIPAA compliance, and protect critical clinical and business services from disruptions that annual assessments cannot anticipate
- SIEM integration with vendor audit logs, API events, and identity activities enables correlation-based alerting for high-risk signals including unusual logins, spikes in PHI access, abnormal data transfers, and configuration changes that deviate from established baselines
- Cloud security posture management and cloud workload protection platforms complement SIEM monitoring by tracking configuration changes and access shifts across vendor environments, with external security ratings services adding an additional layer by scanning vendors' public-facing systems for vulnerabilities and exposed credentials
- Vendor incident response plans must define what constitutes a security incident under HIPAA, assign roles and responsibilities for notification, forensic investigation, containment, and regulatory and patient communications, and establish escalation criteria that trigger enterprise incident response activation for confirmed PHI exposure or clinical system impact
- Vendor contracts must specify notification SLAs requiring 24-hour breach notification regardless of HIPAA's 60-day maximum, because early notification enables containment and investigation before damage escalates and before the organization becomes legally accountable for delays caused by vendor communication failures
- Post-incident reviews within 30 days of every significant event should update vendor risk scores, refine monitoring rules, and adjust playbooks, with repeat critical findings from the same vendor triggering formal re-evaluation of the vendor relationship and potential replacement
What HIPAA-compliant cloud backup and disaster recovery requirements apply to healthcare organizations?
- HIPAA requires maintaining the availability of ePHI as equally to its confidentiality and integrity, meaning backup system failures constitute compliance violations and not merely operational disruptions, with cloud backup vendors required to sign Business Associate Agreements as a prerequisite for receiving any ePHI
- Over 60% of major outages cost more than $100,000 according to the Uptime Institute and organizations with effective backup and disaster recovery processes save approximately $1 million in average breach costs, demonstrating the direct financial return on backup investment beyond compliance obligation
- A 2023 Sophos survey found that while 94% of ransomware victims attempted data restoration from backups, only 57% recovered even half of their data, illustrating the critical gap between having backups and maintaining backup systems that are functional, tested, and reliable under attack conditions
- HIPAA-compliant backup solutions require immutable write-once read-many storage to prevent ransomware encryption or unauthorized deletion of backup copies, along with encryption in transit and at rest, multi-factor authentication for backup administration, and geographic redundancy across multiple physical locations
- Recovery Time Objectives and Recovery Point Objectives must be documented for each critical system and embedded in vendor contracts, with Tier 0 clinical systems such as EHR platforms typically requiring an RTO of four hours and an RPO of 15 minutes that backup architecture must be capable of supporting
- Annual restore testing for all critical systems and more frequent testing for Tier 0 and Tier 1 clinical systems is required to close the gap between having backups and having reliable recovery capability, with test results incorporated into vendor risk assessments and tabletop exercises simulating vendor outages used to validate communication workflows and shared responsibilities
How should healthcare organizations implement and scale a cloud vendor risk management program?
- A phased implementation starting with Tier 0 and Tier 1 vendors such as EHR providers, backup vendors, and medical device manufacturers allows teams to gain experience, refine processes, and demonstrate results before scaling to lower-risk vendor relationships
- Embedding vendor risk management into procurement processes prevents risk from entering the vendor ecosystem by requiring security questionnaires, certification reviews, and BAAs before contract execution, addressing the reality that 54% of organizations reported third-party breaches in 2023
- Around 30% of organizations lack dedicated vendor risk assessment staff, making automated platforms essential for distributing assessment work across IT, legal, compliance, procurement, and operations without creating unsustainable manual workloads for any single team
- Censinet RiskOps automates questionnaire distribution, response tracking, and high-risk finding flagging while Censinet AI enables vendors to complete security questionnaires with evidence summarization that accelerates assessment cycles without sacrificing the human oversight required for critical decisions
- Cross-departmental training and stakeholder engagement are essential operational requirements, with role-specific documentation providing senior management with high-level governance insights and front-line staff with detailed procedures for vendor onboarding, security issue escalation, and assessment documentation
- Regular internal audits to identify gaps before external reviews, combined with a structured 90-day action plan focusing first on cataloging Tier 0 and Tier 1 vendors and embedding security requirements into procurement workflows, provide the foundation for scaling toward a mature program that addresses the full vendor population


