Key Metrics For Vendor Security Compliance
Post Summary
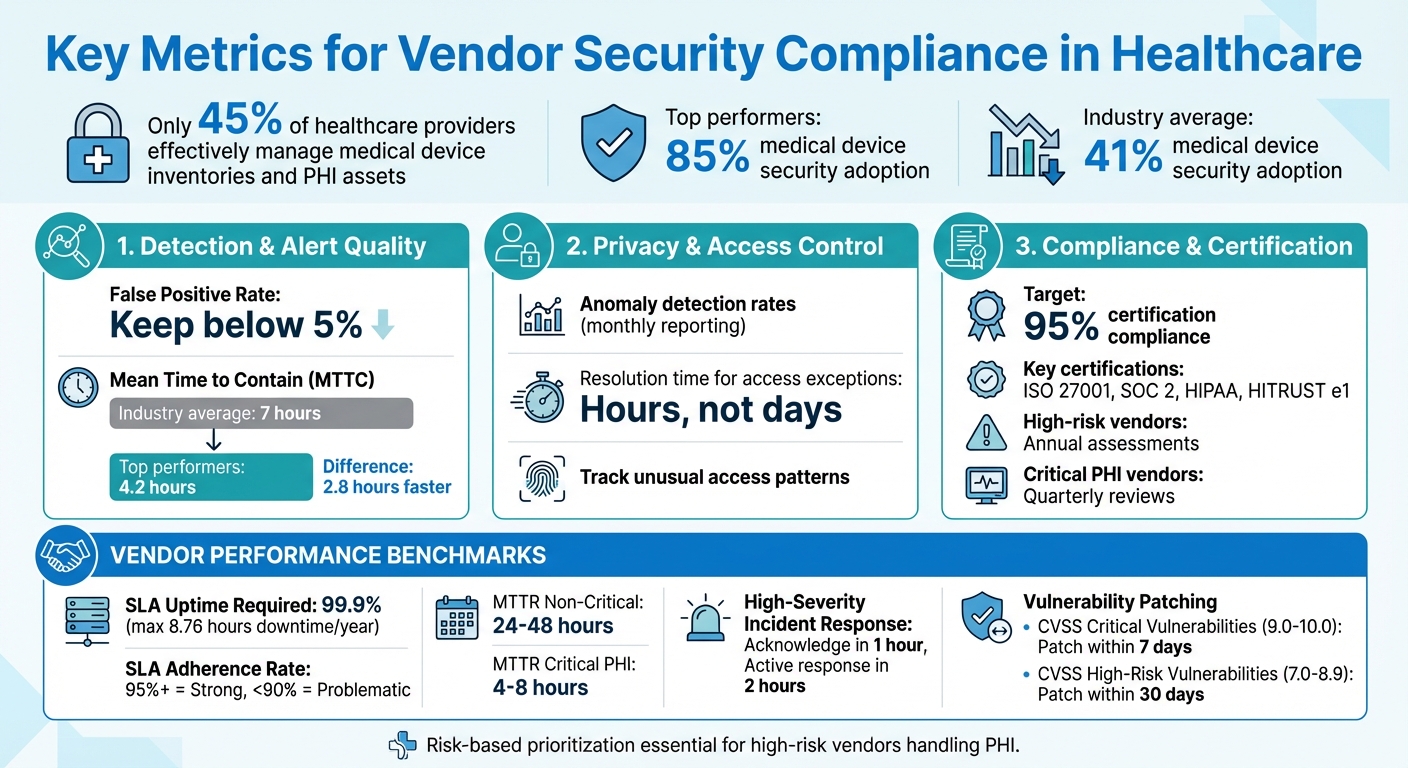
Healthcare organizations face growing risks from third-party vendor risk management for partners handling Protected Health Information (PHI). Without clear metrics, it's hard to ensure vendors meet security standards. Here's what you need to know:
- HIPAA compliance requires vendors to safeguard PHI, but many organizations struggle with oversight.
- Only 45% of healthcare providers effectively manage medical device inventories and PHI assets.
- Top performers achieve 85% medical device security adoption, compared to an industry average of 41%.
To close these gaps, focus on measurable metrics in three areas:
- Threat Detection: Evaluate false positive rates (keep below 5%) and Mean Time to Contain (aim for 4.2 hours).
- Privacy Controls: Track anomaly detection and resolution times for access issues.
- Compliance: Monitor certifications (ISO 27001, SOC 2) and ensure timely risk assessments.
Tools like Censinet RiskOps™ help automate tracking, prioritize risks, and flag underperforming vendors. Tailor oversight based on vendor risk levels, especially for those managing PHI or critical systems.
Healthcare Vendor Security Compliance Metrics and Benchmarks
Mastering Vendor Management | Cybersecurity Vendor Risk Management Training | TPRM
sbb-itb-535baee
Core Metrics for Vendor Security Compliance
Healthcare organizations rely on measurable metrics to ensure vendors meet security standards. These metrics turn vendor compliance into something that can be tracked and managed effectively.
Three main categories of metrics are key for monitoring vendor security: detection and alert quality, privacy and access control, and compliance and certification. Each focuses on a different element of vendor risk - ranging from identifying threats to maintaining recognized certifications. Together, they create a solid framework for evaluating vendor security.
Detection and Alert Quality Metrics
Metrics in this category focus on how well a vendor's security systems can identify and respond to threats.
- True positive and false positive rates: These metrics show how accurately threats are identified. A false positive rate over 5% can overwhelm security teams with unnecessary alerts, increasing the chance of missing real threats. Service Level Agreements (SLAs) should aim to keep false positive rates below this threshold.
- Mean Time to Contain (MTTC): This measures how quickly vendors act after detecting a threat. On average, containment takes 7 hours, but top performers reduce this to 4.2 hours. That 2.8-hour difference can be the line between a minor issue and a major breach. Vendors managing PHI should aim for the faster benchmark.
Privacy and Access Control Metrics
Beyond detection, privacy and access control metrics ensure that Protected Health Information (PHI) remains secure.
- Anomaly detection rates: These track unusual access patterns, such as logins during odd hours or large data downloads. Vendors should report monthly on detected anomalies and how they were investigated.
- Resolution time for access exceptions: This measures how quickly vendors address unauthorized or suspicious access attempts. Ideally, these issues should be resolved within hours, not days. Including these metrics in vendor contracts ensures accountability for safeguarding sensitive data.
Tools like Censinet RiskOps™ can automate the tracking of these metrics, providing real-time insights into vendor behavior and flagging any unusual activity. This automation reduces the workload for security teams while improving monitoring processes.
Compliance and Certification Metrics
Maintaining certifications and adhering to compliance standards is another critical area.
- Certification compliance rates: This tracks the percentage of vendors holding valid certifications like ISO 27001, SOC 2, or HIPAA. It’s essential to not only verify these certifications but also monitor expiration dates and renewal timelines.
- Violation rates: These measure the number of security policy breaches per vendor each quarter, helping identify recurring issues.
- Risk assessment frequency: High-risk vendors should undergo annual assessments, while those handling critical PHI may need quarterly reviews. Additional assessments should be triggered by major incidents or system changes. Setting a goal of 95% certification compliance and timely patching ensures vendors stay on track. For smaller vendors, pursuing HITRUST e1 certification can be a practical step toward broader compliance.
Vendor Performance Metrics
Evaluating vendor performance ensures they deliver on their promises while safeguarding sensitive data. Key metrics offer insights into their reliability and ability to meet critical standards.
Service Level Agreement (SLA) Compliance
SLA compliance metrics assess whether vendors uphold their uptime and remediation commitments. For healthcare, SLAs typically require 99.9% uptime, allowing for just 8.76 hours of downtime annually. Falling short of this can disrupt patient care.
Mean Time to Repair (MTTR) measures how quickly vendors fully resolve issues, distinguishing it from Mean Time to Contain (MTTC), which only tracks initial containment. For non-critical issues, an MTTR of 24-48 hours is common. However, for critical vulnerabilities that could impact Protected Health Information (PHI), resolution should occur within 4-8 hours. Tracking remediation times by severity helps pinpoint vendors struggling with high-priority fixes.
SLA adherence rates reflect overall vendor reliability. This is calculated by dividing the number of commitments met by the total number of commitments. A rate of 95% or higher indicates strong performance, while rates below 90% may signal potential problems.
Incident Response and Vulnerability Management Metrics
Incident response metrics complement SLA data by focusing on vendor preparedness during security incidents. Response times must align with the severity of the threat. For high-severity incidents involving possible PHI exposure, vendors should acknowledge the issue within 1 hour and initiate an active response within 2 hours. Lower-severity incidents may allow for a 4-8 hour response timeframe.
Breach frequency monitors how often vendors face security incidents. Even a single PHI-related breach per year is alarming. Repeated incidents often point to deeper security flaws. Tracking both the number and severity of breaches provides a clearer picture of vendor risk.
Vulnerability scores, based on the Common Vulnerability Scoring System (CVSS), help prioritize fixes. CVSS scores range from 0 to 10, with vulnerabilities rated above 7.0 considered high-risk. Vendors should address critical vulnerabilities (scores 9.0-10.0) within 7 days and high-risk ones (scores 7.0-8.9) within 30 days. Monitoring the percentage of vendors providing evidence of timely patching helps identify those lagging behind.
Tools like Censinet RiskOps™ streamline this process by offering real-time dashboards. These platforms highlight vendors requiring immediate attention, enabling security teams to focus their efforts where it matters most.
Adjusting Metrics Based on Vendor Risk Levels
When it comes to vendor performance metrics, a one-size-fits-all approach doesn’t cut it - especially in healthcare. Different vendors bring different levels of risk, and tailoring oversight based on these risks is a smart way to manage resources effectively. For instance, vendors handling electronic health records (EHRs) or managing medical devices demand much closer monitoring compared to those with minimal risk. By focusing on risk-based metrics, security teams can channel their efforts where they’re most needed, setting clear benchmarks and speeding up responses when necessary.
Risk-Based Metric Prioritization
The first step is sorting vendors into risk categories. High-risk vendors - those with access to protected health information (PHI), connections to critical systems, or control over medical devices - need a deeper dive. These vendors should undergo more frequent assessments, face stricter performance standards, and be monitored for faster detection and resolution of security issues.
Factors like service criticality, network access, PHI exposure, and the potential impact of a failure (concentration risk) are key in determining a vendor's risk level. For example, a vendor managing a large volume of patient data or supporting multiple essential functions should be under tighter scrutiny than others.
Benchmark Examples for High-Risk Vendors
Vendors operating in high-risk areas, like those managing EHRs or clinical applications, must meet rigorous standards. Here’s what that might look like:
- Service Availability: Ensure systems remain operational with minimal downtime.
- Breach Prevention: Employ advanced security measures, including robust access controls like multi-factor authentication for privileged accounts.
- Data Encryption: Use strong encryption for both data at rest and in transit, in line with strict regulatory and industry standards.
- Audit Logging: Maintain comprehensive logs to track activity and detect anomalies.
- Incident Response: Regularly test incident response plans to guarantee quick and effective action when needed.
Platforms such as Censinet RiskOps™ simplify this process by allowing healthcare organizations to fine-tune benchmarks based on vendor risk levels. These tools automatically flag high-risk vendors that fall short of expectations, enabling security teams to focus their efforts where it matters most. This targeted approach ensures critical vendors receive the attention they require, safeguarding essential healthcare operations.
Conclusion
Tracking the right metrics can transform vendor security compliance from a routine task into a powerful tool for healthcare organizations. By focusing on key areas like detection quality, access controls, SLA compliance, and incident response times, security teams get a clear picture of where vendors are meeting standards - and where they’re falling behind. This kind of data-driven oversight doesn’t just improve compliance; it also reduces third-party risks to patient data and care delivery.
There’s still work to be done: for example, medical device security adoption averages just 41%, compared to 85% among top performers. Similarly, the Mean Time to Contain incidents is 7 hours for most, while leaders achieve 4.2 hours.
Risk-based prioritization amplifies the impact of these metrics. By focusing stricter oversight on high-risk vendors - like those handling PHI or managing critical systems - healthcare organizations can allocate resources where they’re needed most. This ensures that security teams aren’t overwhelmed while keeping the highest-risk vendors under close watch.
Tools like Censinet RiskOps™ simplify this process by automating metric tracking, identifying underperforming vendors, and offering centralized dashboards that turn complex data into actionable insights. When healthcare organizations adopt these metrics systematically, they move beyond basic compliance. They create strong vendor ecosystems that safeguard patients, ensure operational stability, and meet regulatory standards with confidence.
The roadmap is clear: define metrics, benchmark progress, adjust oversight based on risk, and monitor continuously. By taking this proactive approach, healthcare organizations can manage vendor relationships effectively, reducing vulnerabilities before they turn into incidents.
FAQs
Which vendor security metrics should we track first?
Begin by keeping tabs on vendor risk ratings, compliance completion rates, and mean time to risk resolution. These core metrics offer crucial insights into your vendors' security practices and allow you to gauge how well your risk management efforts are working.
How do we set metric targets by vendor risk level?
When setting metric targets by vendor risk level, it's all about tailoring benchmarks to the vendor's specific risk tier: critical, high, or moderate. Vendors classified as higher risk often demand stricter standards, such as close to 100% compliance, fast resolution of issues, and constant monitoring. On the other hand, vendors with lower risk levels can have more flexible targets, emphasizing periodic evaluations and general compliance objectives. This tiered system helps allocate resources where they're needed most, improving both security and compliance efforts.
What evidence should vendors provide for HIPAA compliance?
Vendors need to supply comprehensive documentation to confirm their compliance with HIPAA standards. This should include security policies, access logs, breach response records, and Business Associate Agreements (BAAs). Additionally, they should provide details about their encryption practices and evidence of compliance, such as risk assessments, certifications like HITRUST or SOC 2, and regular audit reports. These materials help demonstrate their commitment to meeting HIPAA requirements.


