Common Chain of Custody Mistakes in Cyber Incidents
Post Summary
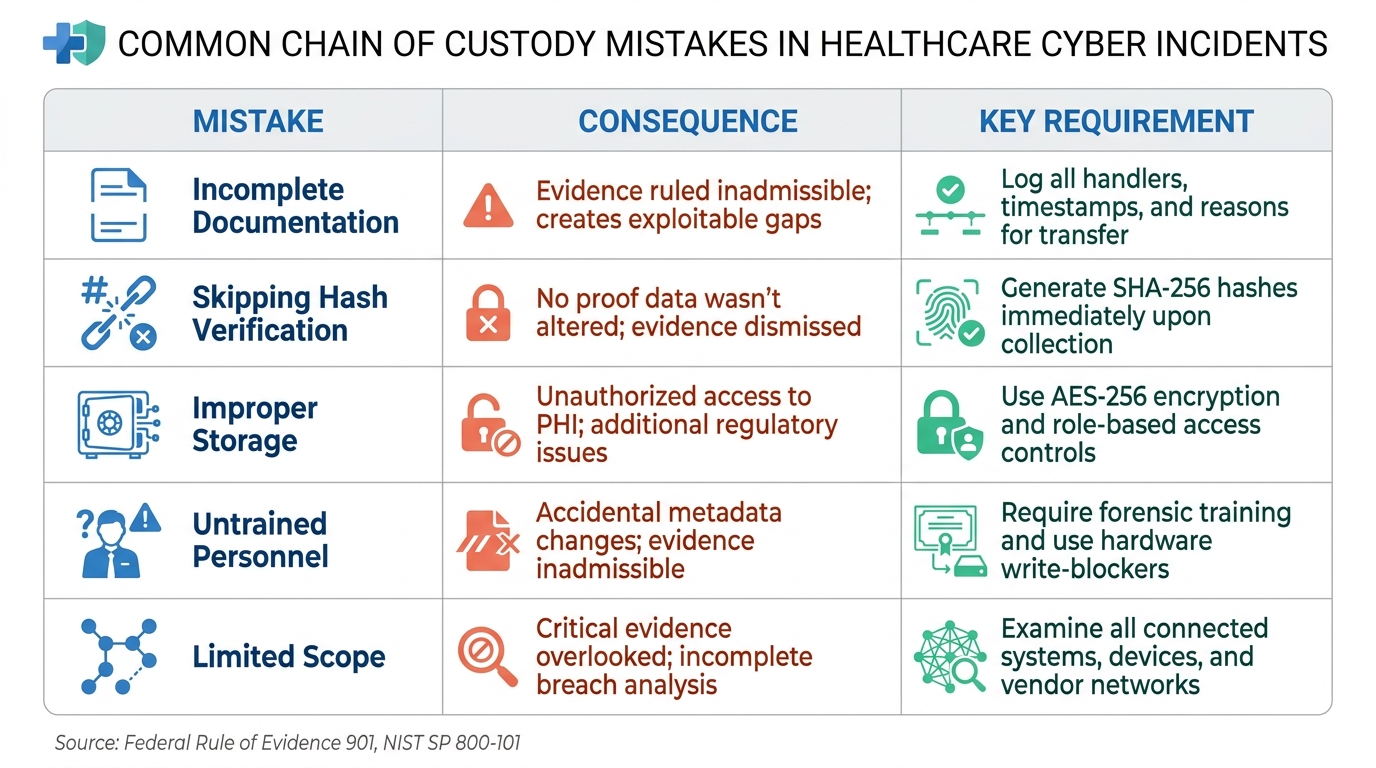
When healthcare organizations face cyber incidents, mishandling digital evidence can lead to legal challenges, regulatory penalties, and loss of patient trust. A chain of custody ensures evidence integrity by documenting every step of its handling. However, common mistakes - like incomplete logs, skipped hash verifications, poor storage practices, and untrained personnel - can render evidence inadmissible in court.
Key takeaways:
- Documentation gaps: Missing logs or incorrect details, like a typo, can raise doubts about evidence authenticity.
- Hash verification: Skipping cryptographic checks (e.g., SHA-256) leaves no proof the data hasn't been altered.
- Storage issues: Storing evidence on insecure devices risks data tampering or breaches.
- Untrained staff: Mishandling evidence or altering metadata can compromise investigations.
- Limited scope: Overlooking interconnected systems (e.g., EHRs, IoT devices) weakens breach analysis.
To avoid these pitfalls, healthcare providers should adopt strict protocols, including detailed documentation, secure storage, trained personnel, and automated evidence management tools like Censinet RiskOps™. These measures help maintain evidence integrity, meet legal standards, and safeguard sensitive patient data.
Digital Forensics Chain-of-Custody Explained | Evidence Handling & Cyber Law Guide
sbb-itb-535baee
Common Chain of Custody Mistakes
5 Common Chain of Custody Mistakes in Healthcare Cyber Incidents
Healthcare organizations face immense pressure during cyber incidents, and errors in handling evidence can derail investigations. Here are some of the most frequent mistakes made when managing the chain of custody.
Incomplete Documentation and Logging Gaps
Every action involving evidence - who handled it, when it was accessed, where it was stored, and why it was transferred - needs to be documented. Missing these details opens the door to legal challenges.
When there are gaps in the timeline, it raises questions. If the location or custody of evidence isn't accounted for, opposing counsel may claim the data was tampered with or even planted [5]. Similarly, failing to log every handoff between personnel, including names, dates, and reasons for transfer, creates missing transfer records that can lead to evidence being dismissed in court [5].
A real-world example highlights the risks. In April 2026, digital forensics expert Thiago Vieira reviewed a case where a typo in logging the serial number of a confiscated laptop caused major confusion in court. Even though the data was intact, the documentation error allowed the defense to argue the evidence might have been swapped, casting doubt on the investigation [6]. Vieira explained:
"Even minor mistakes in documentation or handling can render critical digital evidence inadmissible, risking the loss of prosecution and letting cybercriminals walk free." [6]
To avoid this, log every access to evidence, including who accessed it and why. Overlooked access events can undermine credibility and jeopardize the case [1].
Skipping Evidence Integrity Verification
Calculating cryptographic hash values, like SHA-256, is the standard method to ensure digital evidence hasn’t been altered. This must be done immediately upon collection. If skipped, there’s no mathematical proof that the data remained intact throughout the investigation [4].
In another case reviewed by Vieira, a first responder failed to calculate a cryptographic hash of a seized disk until days later during a fraud investigation involving a Bitcoin wallet. Without a record of who accessed the drive during that time, the evidence was dismissed, stalling the investigation [6].
Hash values are critical because even a tiny change in data - down to a single bit - will result in a different hash, signaling tampering [1]. Without this verification, prosecutors can’t prove the evidence presented in court is identical to what was seized, leading to its dismissal.
Improper Storage and Unauthorized Access
Evidence must be stored securely to prevent unauthorized modifications. This includes using encrypted drives, physical locks, tamper-evident seals, and role-based access controls. Storing evidence on unencrypted drives, personal devices, or shared folders makes it impossible to confirm it wasn’t tampered with during the investigation [1].
Unauthorized access is especially risky because digital files can be altered, copied, or corrupted without leaving visible traces [1]. In healthcare, this risk is heightened by the sensitivity of patient data. Poor storage practices can lead to unauthorized access to protected health information (PHI), potentially triggering regulatory violations on top of the initial breach [1].
Using Untrained Personnel for Evidence Handling
Handling evidence requires specialized training. Staff without forensic expertise can unintentionally destroy critical evidence or break the chain of custody. For example, failing to use hardware write-blockers - essential tools for preventing data modification during access - can compromise evidence [4].
Untrained personnel might also alter metadata, timestamps, or file structures, making it impossible to verify that the evidence remains unchanged. Additionally, they might neglect to generate cryptographic hashes immediately upon collection, which is crucial for proving data integrity. Such errors can lead to evidence being ruled inadmissible under Federal Rule of Evidence 901, which requires proof of authenticity [1].
Another common issue is the lack of proper documentation when evidence is passed between individuals. Every handoff introduces potential legal challenges if not clearly recorded [4].
Limiting the Investigation Scope
Cyber incidents in healthcare often involve more than one system. Electronic health record (EHR) platforms, medical devices, IoT sensors, vendor networks, and cloud storage all generate digital evidence that could be critical for understanding a breach [2].
Overlooking these connected systems is a serious error. For instance, a ransomware attack targeting a hospital’s billing system could have originated through a compromised medical device or a vendor’s portal. Failing to investigate these related systems can leave gaps in understanding the attack vector or identifying all affected data. This weakens the investigation and makes it harder to build a solid case.
A thorough investigation must consider the entire digital ecosystem, including third-party providers and cloud storage, even when spread across different jurisdictions [4].
| Mistake | Consequence | Key Requirement |
|---|---|---|
| Incomplete Documentation | Evidence ruled inadmissible; creates exploitable gaps [5] | Log all handlers, timestamps, and reasons for transfer [5] |
| Skipping Hash Verification | No proof data wasn’t altered; evidence dismissed [4] | Generate SHA-256 hashes immediately upon collection [4] |
| Improper Storage | Unauthorized access to PHI; additional regulatory issues [1] | Use AES-256 encryption and role-based access controls [1] |
| Untrained Personnel | Accidental metadata changes; evidence inadmissible [4] | Require forensic training and use hardware write-blockers [4] |
| Limited Scope | Critical evidence overlooked; incomplete breach analysis [2] | Examine all connected systems, devices, and vendor networks [4] |
Best Practices for Maintaining Chain of Custody
Healthcare organizations can avoid common chain of custody errors by adopting structured procedures that safeguard evidence from the moment it's collected until it's presented in court. These measures address lapses in documentation, integrity, and storage that can undermine forensic investigations. The solution lies in combining standardized documentation, secure storage, skilled personnel, and automated tools to close gaps and bolster legal defensibility.
Creating Detailed Documentation Procedures
Evidence moves through six key stages: collection, documentation, packaging/sealing, preservation/storage, transfer, and analysis [7]. At each stage, specific details must be recorded to address five critical questions: Where is the evidence? How was it obtained? When was it collected? Who handled it? Why was it accessed? [2]
To ensure clarity, use standardized intake forms to capture essential details like case numbers, investigator names, evidence descriptions, physical condition, and initial photographs [4]. Dual-signature logs should document every handoff, including the date, time, and purpose of the transfer [7]. This eliminates uncertainty about who had custody at any given time.
Generate and verify cryptographic hashes (e.g., SHA-256 or MD5) immediately upon collection [7][4]. As noted in Behind the Crime Scene:
"Courts rely on these numbers [hash values] more than human testimony because math does not lie." – Behind the Crime Scene [7]
It's equally important to require personnel to document specific reasons for accessing, exporting, or sharing evidence [1]. A simple handwritten logbook can serve as a backup in case of software failures or power outages [7].
| Documentation Field | Requirement |
|---|---|
| Date and Time | Precise to the minute of collection or transfer |
| Custodian Info | Full name and identification/badge number |
| Location | Exact physical address, room number, or cloud file path |
| Item Description | Serial numbers, model, and distinguishing marks |
| Hash Value | Cryptographic proof (e.g., SHA-256) generated at collection |
| Purpose | Clear reason for the transfer (e.g., "analysis in lab") |
Once documentation is in place, the next step is securing evidence storage.
Using Secure Storage and Access Controls
Evidence must be stored in facilities with controlled access, entry logs, and proper safeguards for digital media. Encrypt all files at rest using AES-256 to ensure they cannot be accessed outside authorized systems [1].
Role-Based Access Control (RBAC) should be implemented to assign permissions, and Multi-Factor Authentication (MFA) should be enforced for all users. Evidence should be stored in separate, case-specific repositories to prevent cross-contamination.
For physical evidence, tamper-evident packaging and seals are critical. Mobile devices should be placed in Faraday bags immediately upon seizure to prevent remote wiping or unauthorized synchronization [7][4]. When accessing storage devices, hardware write-blockers should be used [4].
To preserve the integrity of digital evidence, investigators should never work on original media. Instead, create a forensic image (an exact bit-for-bit copy) and verify it against the original using hash values [7][1]. This ensures the original remains untouched while analysis occurs on the replica.
Training Staff in Forensic Evidence Handling
Gaps in manual recordkeeping and procedural knowledge are often the root causes of chain of custody failures [1]. Regular training equips staff to meet authentication standards under Federal Rule of Evidence 901 and prevents evidence from being deemed inadmissible [1][4].
Training programs should cover:
- Initial preservation techniques, including the use of write-blockers, Faraday bags, and tamper-evident packaging
- Accurate documentation practices, such as completing chain of custody forms and recording timestamps
- Hash verification methods, including generating and comparing MD5 and SHA-256 hashes
- Legal standards, such as FRE 901, 902, and 702
- Secure handling protocols, including encrypted storage and access controls
- Best practices for forensic imaging, such as creating and verifying bit-for-bit replicas
Limiting the number of individuals who handle evidence can further reduce complexity and minimize vulnerabilities [4].
Automated tools can complement staff training and improve evidence integrity.
Using Digital Evidence Management Tools
Switching from manual processes to Digital Evidence Management Systems (DEMS) can significantly reduce human error in recordkeeping [1]. DEMS automate time-stamped audit trails and hash re-verifications, ensuring that evidence integrity is maintained throughout an investigation.
These tools also make it easy to retrieve specific evidence or review the custody history using searchable metadata and logs. Emerging technologies like permissioned blockchains are now being used to create immutable records of collection events, custody transfers, and hash verifications [4].
Healthcare organizations should align their procedures with standards such as NIST SP 800-101 Revision 1 for technical validation and NIST SP 800-86 for forensic technique integration [7][4].
Platforms like Censinet RiskOps™ offer healthcare organizations tools to manage cyber incidents, including automated evidence tracking and collaborative risk management features. With AI-powered integrity verification, these systems ensure evidence remains unaltered, while centralized documentation supports compliance with healthcare regulations related to PHI and patient data.
How Censinet Supports Chain of Custody Management
Healthcare organizations face a tricky balancing act when managing the chain of custody for sensitive data. Censinet RiskOps™ steps in to simplify this process, addressing issues like missing documentation, storage weaknesses, and human errors that could jeopardize forensic investigations. Let’s break down how automated tracking, team collaboration, and AI-driven verification work together to protect evidence integrity.
Automated Evidence Tracking and Logging
Forget juggling spreadsheets and email chains - Censinet RiskOps™ introduces a seamless, automated system that keeps everything in check. The platform’s Cybersecurity Data Room™ creates a detailed, permanent record of every evidence-handling activity [9]. It even generates Corrective Action Plans (CAPs) to pinpoint security issues and track their resolution, ensuring a complete and verifiable history of risk management efforts [9]. This streamlined approach speeds up assessments and remediation while covering risks across all third-party relationships [9].
Real-time Risk Flags step in to alert teams when critical documents, like Business Associate Agreements (BAAs), are missing, keeping the chain of custody intact [9]. Plus, delta-based reassessments focus only on new or updated information, ensuring the evidence log stays accurate [9]. Tower Health saw the benefits firsthand, as CISO Terry Grogan shared:
"Censinet RiskOps allowed 3 FTEs to go back to their real jobs! Now we do a lot more risk assessments with only 2 FTEs required." – Terry Grogan, CISO, Tower Health [8]
Collaborative Risk Management for Incident Response
Censinet RiskOps™ doesn’t just stop at tracking - it also makes teamwork more efficient. When incidents occur, coordinating between teams, vendors, and stakeholders is critical. The platform facilitates this with a network that connects over 50,000 vendors and products in the healthcare sector [8]. Its Digital Risk Catalog™ includes over 40,000 pre-assessed and risk-scored vendors, speeding up the process of verifying third-party security during investigations [9].
Censinet AI™ plays a key role here, automatically directing assessment results and tasks to the right people for action [8]. Baptist Health saw a major improvement by ditching spreadsheets in favor of this system. As James Case, VP & CISO of Baptist Health, put it:
"Not only did we get rid of spreadsheets, but we have that larger community [of hospitals] to partner and work with." – James Case, VP & CISO, Baptist Health [8]
AI-Powered Integrity Verification
To keep evidence secure, Censinet RiskOps™ uses SHA-256 technology to create unique digital fingerprints for every file [1]. If even a tiny piece of data changes, the hash value shifts, making tampering easy to catch.
The platform also builds immutable audit trails that log every interaction, complete with timestamps and user details [1][10]. These records align with Federal Rule of Evidence 901, which requires proper authentication for evidence to be admissible in court [1]. Files are further safeguarded with AES-256 encryption, and multi-factor authentication ensures access is limited to authorized personnel [1].
On top of that, AI-powered tools send automated alerts if unauthorized changes are detected [1]. The platform’s efficiency is impressive - it reduces reassessment time to under a day [9]. This quick turnaround helps healthcare organizations respond faster to incidents while maintaining the high documentation standards needed for legal proceedings.
Conclusion
The challenges discussed highlight just how crucial proper evidence management is for healthcare cybersecurity. Issues like documentation gaps, poor storage practices, or untrained staff can make critical digital evidence unusable in court - potentially allowing cybercriminals to avoid consequences. As digital forensics expert Thiago Vieira pointed out, even small errors in documentation or handling can put entire prosecutions at risk [6].
The numbers speak for themselves: 66% of law enforcement professionals now see digital evidence as more important than physical evidence [3], and ransomware damages have exceeded ransomware damages have exceeded $11 billion1 billion in a single year [2]. It's clear that healthcare organizations must make managing the chain of custody a top priority.
By tackling these recurring issues with forward-thinking solutions, healthcare providers can strengthen both their legal defenses and their ability to respond to incidents effectively. Tools like Censinet RiskOps™ offer automated evidence tracking with cryptographic hash verification and immutable audit trails that align with Federal Rule of Evidence 901 standards. This eliminates the risk of manual documentation errors while providing the speed and precision teams need during high-stakes incidents [3].
Now is the time to implement strong protocols to protect investigations and safeguard patient data.
FAQs
What’s the fastest way to start a defensible chain of custody during an incident?
To maintain a reliable chain of custody, it's crucial to act fast in documenting and preserving digital evidence. Start by recording essential details such as device descriptions, collection methods, and timestamps. Tools like write-blockers can help prevent data alteration, while tamper-evident packaging ensures the evidence remains secure. Be sure to log every action taken during the process. Quick and precise actions like these protect the integrity of the evidence and reduce the chances of errors that could compromise its admissibility in legal proceedings.
How often should hashes be re-verified after evidence is collected?
Hashes need to be consistently re-verified during evidence handling, particularly after any transfer or interaction with the data. This process ensures the integrity of the information, helping to quickly identify any signs of tampering or inconsistencies. By doing so, potential problems with the chain of custody can be avoided.
Which connected systems are most often overlooked in healthcare breach investigations?
In healthcare breach investigations, certain connected systems often don't get the attention they deserve. These include:
- Gaps in digital evidence records: Missing pieces in the evidence trail can make it harder to piece together what happened.
- Missing logs: Without complete logs, investigators may struggle to identify the source or extent of a breach.
- Unexplained access events: Instances of unauthorized or unusual access can go unnoticed, leaving critical questions unanswered.
- Mismatched hashes: When file hashes don’t align, it raises concerns about data integrity and tampering.
These oversights can disrupt the chain of custody and create serious roadblocks during an investigation.


