Secure Email Protocols for HIPAA Compliance
Post Summary
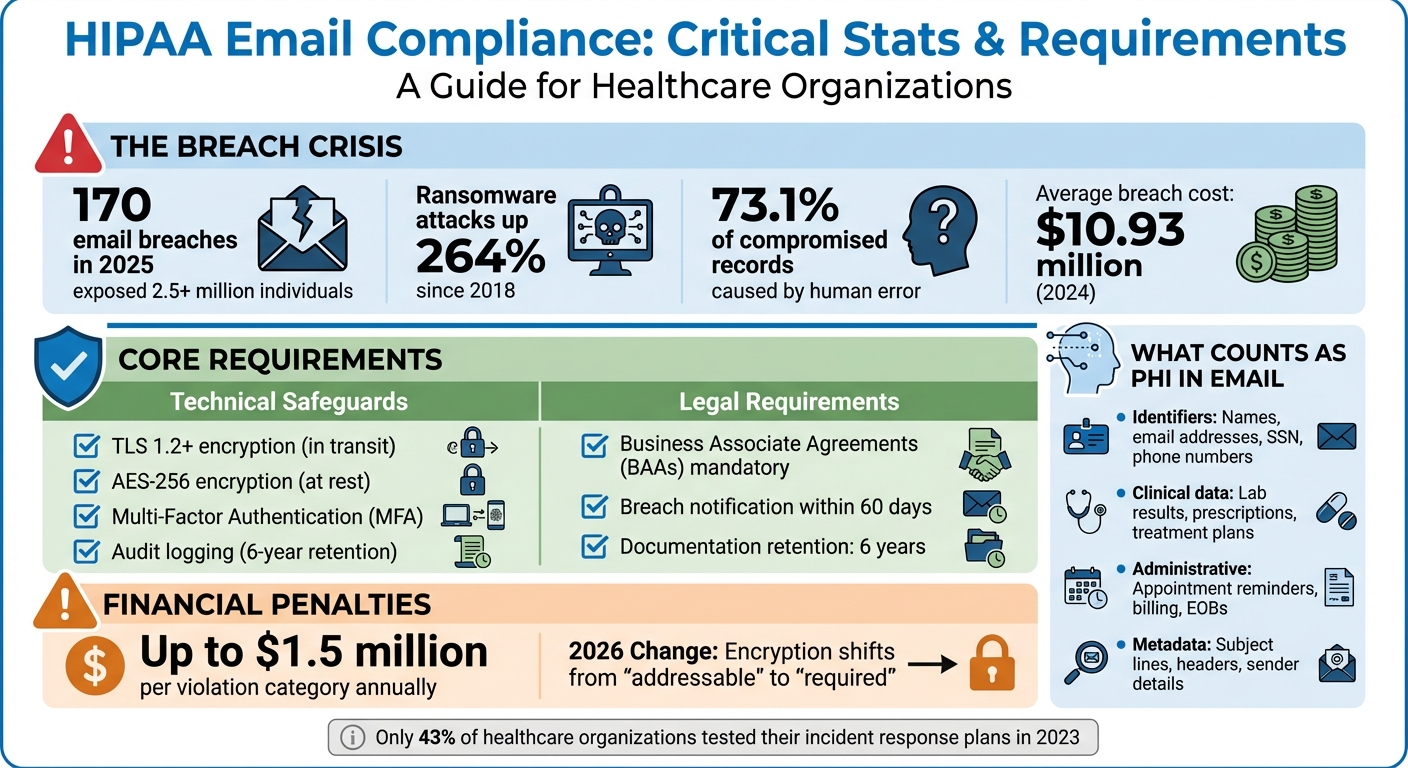
Email is one of the riskiest areas for HIPAA compliance. In 2025, 170 email-related breaches exposed data of over 2.5 million individuals, costing healthcare organizations millions. With ransomware attacks up 264% since 2018 and human error accounting for 73.1% of compromised records, secure email practices are no longer optional.
Here’s what you need to know:
- HIPAA mandates encryption for emails containing Protected Health Information (PHI) during transmission and storage. Starting in 2026, encryption will shift from "addressable" to "required."
- Key technical safeguards include enforced TLS 1.2+, AES-256 encryption, Multi-Factor Authentication (MFA), and audit logging.
- Business Associate Agreements (BAAs) are mandatory with third-party vendors handling PHI, even if encryption is in place.
- Staff training and risk assessments are critical to preventing breaches caused by human error or phishing attacks.
- Incident response plans must be ready to address breaches quickly, with notifications to affected individuals and HHS within HIPAA’s strict timelines.
Failing to meet these standards can result in fines up to $1.5 million per violation category annually, along with reputational damage and loss of patient trust. By implementing secure email protocols, healthcare organizations can protect sensitive data and maintain compliance.
HIPAA Email Compliance: Key Statistics, Requirements & Penalties 2025
How to make your email HIPAA compliant
sbb-itb-535baee
HIPAA Email Requirements Explained
HIPAA allows healthcare providers to use email for communication, but only if protected health information (PHI) is adequately secured. The Security Rule emphasizes the need for technical safeguards like encryption and decryption of electronic PHI (ePHI). While encryption is considered "addressable" rather than mandatory, it means you must either encrypt, implement an equivalent safeguard, or document why encryption isn't feasible [5]. The Privacy Rule also permits email communication with patients, provided "reasonable safeguards" are in place, such as verifying email addresses and limiting the amount of disclosed information [4].
"While the Privacy Rule does not prohibit the use of unencrypted e-mail for treatment-related communications between health care providers and patients, other safeguards should be applied to reasonably protect privacy." – U.S. Department of Health and Human Services (HHS) [4]
If a third party handles PHI, you must secure a Business Associate Agreement (BAA) with them, regardless of whether encryption is used [4][6]. Without this agreement, your email system cannot be considered HIPAA-compliant. This is a critical component of third-party risk management for healthcare providers.
"Without a BAA, even a fully encrypted service is not HIPAA compliant." – Paubox [4]
HIPAA also requires access controls to limit who can view PHI, audit controls to track email activity, and adherence to the minimum necessary standard, ensuring only essential PHI is shared [4][7]. Organizations must also retain compliance-related documentation, such as security policies and email logs, for six years [6].
To fully grasp the requirements, it's essential to understand what qualifies as PHI in an email context.
What Counts as PHI in Email?
PHI includes any identifiable health information linked to a patient's care, payment, or treatment. Even an email address - one of HIPAA's 18 identifiers - becomes PHI when paired with clinical details, such as a message from a specialist to a patient [7].
Examples of PHI in email include:
- Identifiers: Names, email addresses, phone numbers, Social Security numbers, and account numbers.
- Clinical Context: Lab results, treatment plans, prescriptions, or referrals.
- Administrative Data: Appointment reminders, billing details, or Explanation of Benefits (EOB) forms.
- Metadata: Subject lines, sender/recipient fields, and message headers.
For instance, a subject line like "John Smith's diabetes test results" exposes PHI before the email is opened, as headers are often not encrypted end-to-end [6]. Attachments, such as x-rays or prescriptions, also qualify as PHI.
| PHI Component | Examples in Email Context |
|---|---|
| Identifiers | Patient name, email address, phone number, SSN |
| Clinical Context | Lab results, treatment plans, prescriptions |
| Administrative Data | Appointment reminders, billing statements, EOBs |
| Metadata | Subject lines, message headers, sender details |
Required Technical Safeguards for Email
HIPAA's Security Rule outlines five essential technical safeguards for email systems that handle ePHI. Encryption is a top priority - data must be protected both "at rest" (stored in mailboxes or archives) and "in transit" (while being transmitted). For stored data, use AES-128 or stronger encryption, following NIST SP 800-111 guidelines [5]. For emails in transit, protocols like TLS 1.2 or higher, or FIPS 140-2 validated methods such as S/MIME, PGP, or OpenPGP, are recommended [5].
"The HIPAA compliance email encryption rules are that emails containing electronic Protected Health Information (ePHI) must be encrypted at rest and in transit unless encryption is assessed not to be a reasonable and appropriate safeguard to protect PHI, in which case an equally effective alternative measure must be deployed." – Defensorum [5]
Other key safeguards include:
- Access Controls: Limit access to PHI using unique user IDs, strong passwords, and Multi-Factor Authentication (MFA) [4].
- Audit Controls: Track access and activity through system logs.
- Integrity Controls: Use digital signatures or checksums to confirm PHI hasn't been altered.
- Transmission Security: Protect data from interception during transit using secure protocols.
| Safeguard Type | Implementation Specification | Purpose |
|---|---|---|
| Access Control | Unique User IDs, MFA, Auto Logoff | Restrict PHI access to authorized users |
| Audit Controls | Activity Logs, Entry/Exit Tracking | Record who accessed PHI and when |
| Integrity | Digital Signatures, Checksums | Ensure PHI remains unaltered |
| Transmission Security | TLS 1.2+, S/MIME, PGP | Prevent data interception during transit |
HIPAA's "technology neutrality" approach means you can choose your tools, as long as they meet the required security standards [5]. Regular risk assessments help identify vulnerabilities, and decisions regarding encryption must be thoroughly documented. If encryption isn't used, you must demonstrate that an alternative measure offers equivalent protection and justify why encryption isn't practical for your setup [5].
These technical safeguards are the foundation of secure email practices under HIPAA, guiding the selection of compliant tools and configurations discussed in subsequent sections.
How to Choose a HIPAA-Compliant Email Provider
Picking the right email provider is crucial for protecting sensitive patient information, also known as PHI (Protected Health Information). A poor choice can lead to data breaches, hefty fines, and legal troubles. Not every email service meets HIPAA standards, and even popular platforms may require specific configurations or paid plans to comply.
For example, only paid enterprise plans - like Google Workspace and Microsoft 365 - offer configurations for HIPAA compliance and include signed Business Associate Agreements (BAAs). Free versions like Gmail or Outlook are not compliant [8][9].
"Without a BAA, even secure platforms are not HIPAA compliant" – Gil Vidals, CEO of HIPAA Vault [8]
Beyond having a signed BAA, your email provider must support encryption for data both in transit and at rest [8]. Features like Multi-Factor Authentication (MFA) and audit logs (kept for at least six years) are mandatory under HIPAA rules. Additionally, tools for Data Loss Prevention (DLP) are critical - they automatically encrypt or block emails containing PHI [8].
When reviewing providers, check their technical safeguards. Some systems fall back to plain text if the recipient's server doesn’t support TLS encryption, which compromises security. Instead, configure your email to block delivery or redirect to a secure portal [10]. Look for providers with HITRUST certification, as this third-party standard validates their security measures. Less than 1% of HITRUST-certified organizations reported breaches over a two-year span [2].
Finally, assess the provider's technical and administrative controls to ensure they meet all HIPAA requirements.
Required Features for HIPAA-Compliant Email
Once you’ve secured a legally binding BAA, confirm that your provider includes the necessary technical features. Encryption should be automatic, not something users need to activate manually. This helps prevent human error, which caused 73.1% of all records compromised in breaches during 2025 [2].
Key features to look for include:
- Automatic encryption (both in transit and at rest)
- Strong access controls, like MFA and Role-Based Access Control (RBAC)
- Secure archiving with audit logging for at least six years
- Message integrity verification through digital signatures like S/MIME or PGP
If you’re using platforms like Microsoft 365 or Google Workspace, disable outdated protocols like IMAP and POP3. These older systems can bypass modern security measures [9].
| Feature | HIPAA Requirement Category | Technical Standard/Example |
|---|---|---|
| Encryption in Transit | Addressable (effectively required) | TLS 1.2 or 1.3 |
| Encryption at Rest | Addressable (effectively required) | AES 256-bit |
| Authentication | Required | Multi-Factor Authentication (MFA) |
| Audit Controls | Required | Logs retained for 6 years |
| Legal Framework | Required | Signed Business Associate Agreement |
Pricing varies widely among providers. For instance, HIPAA Vault offers managed compliant hosting starting at $120/month. Other services like Paubox and Hushmail include BAAs with all paid plans, while Virtru may require a specific upgrade to add BAA support [8][11].
Getting a Business Associate Agreement (BAA)
Once you’ve confirmed the technical features, the next step is securing a solid BAA. This agreement shifts some responsibility for PHI protection to your email provider and outlines their obligations under HIPAA laws. A BAA must be actively signed or accepted electronically within your account settings [2].
A valid BAA must cover at least ten key legal requirements, such as:
- Scope of PHI protection
- Permitted uses and disclosures
- Safeguard requirements
- Breach notification procedures
- Subcontractor arrangements [2]
Before signing, double-check that the provider’s HIPAA compliance features are clearly stated in the BAA. Document this verification in your organization’s risk analysis [2].
Providers like Google and Microsoft offer detailed HIPAA implementation guides. These resources explain how to configure your account for compliance, so ensure your chosen plan supports HIPAA settings.
The BAA should also address data retention and destruction. HIPAA mandates that electronic PHI be kept for at least six years. Some states or Medicare rules may require retention for seven years [11]. Verify that your provider’s archiving system meets these standards and includes secure data destruction procedures once the retention period ends.
Lastly, remember that signing a BAA doesn’t mean you’re off the hook for compliance. You’re still responsible for regular risk assessments, staff training, access controls, and system monitoring. The BAA ensures your provider shares liability for protecting PHI within their platform [8][9].
Setting Up Email Encryption Protocols
Once you've chosen a HIPAA-compliant email provider and signed a Business Associate Agreement (BAA), the next step is configuring encryption protocols. HIPAA requires encryption when it's feasible - or documentation of alternative safeguards if encryption isn't possible. For any organization handling Protected Health Information (PHI), encryption is a must.
You'll need to implement two key types of encryption: in-transit encryption (securing emails as they travel between servers) and at-rest encryption (protecting stored messages in mailboxes and archives). For in-transit security, the standard is Transport Layer Security (TLS) 1.2 or higher. For at-rest encryption, Advanced Encryption Standard (AES) with 256-bit keys is widely used.
For high-risk communications, like those with business partners or other healthcare organizations, consider adding message-level encryption through protocols such as S/MIME or PGP. These encrypt the actual message content, offering end-to-end security - even if a mail server is compromised. When communicating with patients, a secure portal is often the safest option. With this approach, the email contains only a notification link, and the recipient must log into a secure portal to view PHI. This method ensures protection during both transmission and storage.
Types of Encryption Protocols and Their Uses
Different encryption methods address different needs:
| Protocol/Method | Primary Use Case | How It Works | When to Use It |
|---|---|---|---|
| TLS (1.2+) | In-Transit | Encrypts the connection between email servers during transmission | Standard for server-to-server email; prevents cleartext fallback |
| S/MIME / PGP | Message-Level | Secures message content and attachments using digital certificates/keys | Best for high-risk exchanges, ensuring content integrity and sender authentication |
| AES-256 | At-Rest | Encrypts stored data on disks, databases, or cloud services | Essential for archived emails and mailbox data |
| Secure Portal | Patient Communication | Sends a notification link while keeping PHI on a secure server | Ideal for patient communication to maintain control over PHI access |
The key difference lies in where the encryption is applied. TLS protects data during transmission, S/MIME and PGP secure the content itself, and AES-256 safeguards stored information. For most healthcare organizations, enforced TLS combined with AES-256 covers the basics, while message-level encryption or secure portals are used for particularly sensitive exchanges.
How to Configure Encryption Settings
Start by enforcing TLS 1.2 or higher on your mail servers. Configure your system to reject or redirect messages to a secure portal if the recipient's server cannot establish a secure connection. It's critical to avoid allowing a "silent downgrade" to cleartext if the recipient's server lacks TLS support.
"HIPAA is risk-based and does not mandate a single method. Use enforced Transport Layer Security (TLS) for in-transit protection and message-level encryption (S/MIME, PGP, or a secure portal) for external recipients."
– AccountableHQ
Disable outdated protocols like SSL 2.0, SSL 3.0, TLS 1.0, and TLS 1.1. The National Security Agency strongly advises replacing these with modern encryption standards. If you're using platforms like Microsoft 365 or Google Workspace, you can typically adjust these settings in the admin console under security or compliance.
Implement Data Loss Prevention (DLP) rules to scan for PHI identifiers. DLP automation can trigger encryption or redirect emails to a secure portal, reducing the risk of human error.
For at-rest encryption, confirm that your provider uses AES-256 for mail storage and archives. If you're managing your own mail servers, ensure proper key management practices, such as segregated key storage, regular key rotation, and using FIPS-validated modules. Additionally, deploy Mail Transfer Agent Strict Transport Security (MTA-STS) to prevent man-in-the-middle attacks that could force emails to be sent in cleartext.
Finally, test your setup by sending emails to external domains and checking the email headers to confirm TLS negotiation. This ensures your encryption protocols are functioning as intended.
Setting Up Access Controls and Monitoring
Encryption by itself isn’t enough to keep your email system in line with HIPAA standards. You also need to manage who can access PHI (Protected Health Information) and monitor how it’s used. Weak access controls have been at the center of recent breaches, highlighting the importance of this aspect [13].
According to HIPAA’s Security Rule, organizations must implement unique user IDs, emergency access procedures, automatic logoff, audit controls, and authentication mechanisms (45 CFR 164.312) [15]. This means every staff member should have their own login credentials, multi-factor authentication (MFA) should be enforced, and all actions involving ePHI must be logged. The proposed 2025 Security Rule update is set to make MFA a mandatory requirement rather than an optional measure [13]. While encryption protects data, strong access controls and consistent monitoring are essential for maintaining compliance.
Configuring Role-Based Access Controls
Start by mapping out job roles and limiting access to only what’s necessary for each position. For example, a billing clerk doesn’t need to see clinical notes, and nurses shouldn’t have the ability to export the entire patient database. This approach, known as the least privilege principle, ensures access is granted only when there's a documented need [15].
- Assign unique user IDs to every employee, eliminating shared credentials to ensure accountability [15].
- Set up workflows to manage access when employees join, change roles, or leave the organization [13][15].
- Conduct quarterly access reviews with managers to identify and fix any inconsistencies [15].
To further tighten security, restrict or disable auto-forwarding to external or personal email accounts. This feature is a common way for data to be silently exfiltrated [13][14]. Additionally, monitor and allowlist third-party apps that request broad permissions, like reading email content via OAuth grants [13]. For emergencies, establish a "break-glass" process that logs access reasons and notifies compliance [15].
Finally, bolster these measures with robust multi-factor authentication.
Setting Up Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring two verification factors: something the user knows (like a password) and something they have (like a one-time code or biometric) [16][17]. Even if a password is compromised - phishing accounts for 80%–95% of attacks [19] - MFA can block unauthorized access.
"Two-factor authentication (2FA) is a critical component of HIPAA compliant email systems, as it adds an additional layer of security to protect sensitive patient information from unauthorized access." – Tshedimoso Makhene, Author [16]
Here’s how to implement MFA effectively:
- Enforce MFA for all user and administrator accounts [14][10].
- Use authenticator apps that generate time-based one-time passwords (TOTP) instead of SMS-based codes, which are more vulnerable to interception [16].
- Disable outdated authentication protocols that don’t support MFA, as they can be exploited by attackers [10].
- Configure conditional access policies to require additional MFA challenges for sign-ins from unusual locations or risky behavior [10][3].
- Require MFA on all devices accessing your email system [16][10].
In addition to deploying MFA, train your staff to use it correctly and recognize social engineering attempts aimed at stealing authentication codes [16][10].
Audit Logging and Activity Monitoring
HIPAA mandates under 45 CFR §164.312(b) that organizations record and examine activity in systems containing ePHI [18][14]. These logs should capture critical details such as the "Who" (unique user ID), "What" (actions like viewing or exporting patient data), and "When/Where" (timestamps and source IP addresses) [15].
"Healthcare organizations rarely fail HIPAA audits simply because a breach occurred. More often, they fail because they cannot prove what happened." – Gil Vidals, CEO, HIPAA Vault [18]
To meet these requirements:
- Use a Security Information and Event Management (SIEM) platform to collect logs from across your systems and turn raw data into actionable insights [18].
- Set up real-time alerts for high-risk activities like unauthorized forwarding rules, mass downloads, or attempts to delete logs [18][14][12].
- Store logs in write-once or immutable storage to prevent tampering, and keep them for at least six years to comply with HIPAA’s documentation rule [18][14].
- Don’t just collect logs - review them quarterly to detect and address issues proactively [18][10].
Proactive monitoring not only speeds up breach detection but also discourages insider threats, as employees know their actions are being tracked [18].
For organizations looking to simplify compliance and enhance security monitoring, tools like Censinet RiskOps™ (https://censinet.com) can provide integrated risk management solutions. By putting these access controls and monitoring practices in place, you create a layered defense system essential for HIPAA-compliant email operations.
Staff Training and Risk Assessments
Even with advanced email controls in place, mistakes by staff can undermine their effectiveness. Human error continues to be a major factor in email-related HIPAA violations, whether it’s sending messages to the wrong recipient or falling for phishing scams. To stay compliant with HIPAA, regular training and thorough risk assessments are non-negotiable.
Training Staff on Secure Email Practices
A one-size-fits-all annual training session isn’t enough. Effective training should be tailored to the specific roles of your staff. For example, a billing clerk and a clinician have different workflows involving PHI, and their training should reflect those differences.
Start with the basics: help your team recognize PHI and emphasize the importance of using only the minimum necessary information. Provide email templates that exclude unnecessary identifiers and encourage the use of secure links instead of attachments.
Phishing simulations are another powerful tool. Regularly test your staff’s ability to spot phishing attempts, and provide immediate feedback and coaching for anyone who fails. Focus on the tactics commonly used to target healthcare organizations, such as credential theft and patient data scams.
Your training should also cover these key areas:
- When to use enforced TLS or switch to secure messaging portals
- How to manually activate encryption for sensitive communications
- The importance of double-checking recipient addresses, especially when autocomplete suggests external domains
- The protocol for reporting mistakes or suspicious messages (usually by contacting the Privacy Officer)
| Training Topic | Key Learning Objective |
|---|---|
| PHI Recognition | Identify sensitive information that must be protected in emails and attachments. |
| Encryption Tools | Learn how to manually encrypt emails or use secure messaging portals. |
| Recipient Verification | Practice verifying external addresses and managing distribution lists. |
| Incident Reporting | Understand who to contact immediately after an error or suspicious activity is detected. |
| Subject Line Hygiene | Ensure subject lines remain neutral and free of patient-identifiable information. |
Reinforce the rule that PHI must never be forwarded to personal email accounts. Staff should only use approved systems covered by Business Associate Agreements (BAAs) for storing or transmitting PHI. Mobile devices used for work must have Mobile Device Management (MDM) features, such as screen locks and remote wiping. Document all training sessions, including any disciplinary actions for non-compliance, and retain these records for at least six years as required by HIPAA [20][21].
While training builds awareness, regular risk assessments are crucial for identifying and addressing vulnerabilities in your email security practices.
How to Conduct Email Risk Assessments
Email security is a cornerstone of HIPAA compliance, and regular risk assessments help ensure your safeguards remain effective. A comprehensive assessment should look at every stage of PHI handling - collection, composition, transmission, storage, retrieval, and disposal. Treat this as an ongoing process, not a one-time task. Maintain a risk register that identifies potential email threats and the controls in place to mitigate them.
Key areas to evaluate include unauthorized mailbox access, excessive forwarding, and the use of unmanaged devices. Monitor Data Loss Prevention (DLP) alerts for signs of policy violations or attempts to exfiltrate data. Keep an eye out for unusual login patterns, such as access from unexpected locations or at odd hours. Conduct periodic audits of outbound emails to ensure staff are adhering to the "minimum necessary" standard.
In the event of a potential incident, perform a four-factor breach assessment: determine if PHI was exposed, identify unauthorized access, confirm whether PHI was viewed, and evaluate the risk mitigation steps taken. If a breach is confirmed, notify affected individuals promptly - no later than 60 calendar days from discovery. For breaches involving 500 or more individuals in the same region, you must also notify HHS and the media within the same timeframe [20].
| Risk Category | Specific Email Threat | Recommended Mitigation Control |
|---|---|---|
| Human Error | Misdirected email/Autofill mistakes | Disable autocomplete; require confirmation for external domains. |
| External Attack | Phishing/Credential theft | Use multi-factor authentication (MFA); implement SPF, DKIM, and DMARC protocols. |
| Data Exfiltration | Forwarding to personal accounts | Block external forwarding; use DLP to flag PHI patterns. |
| Unauthorized Access | Lost or stolen mobile devices | Enforce MDM with remote wipe and screen locks. |
| Technical Failure | Encryption downgrade/Cleartext fallback | Require TLS 1.2+ and reroute emails to secure portals if TLS fails. |
Conduct quarterly reviews with department managers to confirm that mailbox access and folder permissions match current job responsibilities. Test encrypted email backups and disaster recovery procedures regularly to ensure they work when needed.
For organizations looking to simplify this process, platforms like Censinet RiskOps™ (https://censinet.com) can centralize risk management efforts. These tools provide a clear overview of email-related risks alongside other cybersecurity concerns. By combining tailored staff training with regular risk assessments, you can build a compliance strategy that evolves with emerging threats.
Creating an Incident Response Plan for Email Breaches
Despite best efforts, breaches can still happen - whether due to human error or increasingly sophisticated phishing attacks. In 2023 alone, the HHS OCR received over 700 breach reports, impacting more than 135 million individuals. Email and phishing accounted for 22% of these large-scale breaches [23]. To make matters worse, the average cost of a healthcare breach soared to $10.93 million in 2024 [10].
Building an Email Breach Response Plan
Start by assembling a cross-functional team with clearly defined roles. This team should include:
- Incident Coordinator: Oversees the response process.
- IT Security Specialists: Handle containment and forensic analysis.
- Compliance Officers: Manage regulatory notifications.
- Legal Counsel: Evaluate the exposure of Protected Health Information (PHI).
Write down each team member’s responsibilities to prevent any confusion during a breach.
Your response plan should also include detailed timelines for each phase. For example, aim to detect breaches within 1 hour, contain the issue within 24 hours, and recover within 48–72 hours [22][23]. If unauthorized email access is detected, IT should immediately isolate the compromised server while compliance assesses the extent of PHI exposure. Make sure to preserve audit logs for forensic purposes and retain them for six years [22][24]. This structured approach ensures the team acts swiftly and in sync.
Test your plan regularly with tabletop exercises that simulate real-world scenarios, like a phishing attack that compromises multiple accounts. These drills will help your team practice detecting breaches, performing their roles, and communicating effectively with stakeholders. Use these exercises to identify and address weak points, such as delays in enforcing multi-factor authentication or unclear notification procedures [25][26]. In 2023, only 43% of healthcare organizations tested their incident response plans, and those that didn’t saw recovery times stretch to an average of 277 days [10].
Reporting Breaches to Patients and Authorities
Under HIPAA's Breach Notification Rule, you must notify affected individuals as soon as possible, but no later than 60 days after discovering a breach [23][24]. For breaches affecting 500 or more individuals, you’re also required to report the incident to the HHS OCR within 60 days and notify the media if more than 500 people in a single state are impacted. Smaller breaches (fewer than 500 individuals) should be logged internally and reported annually by March 31 [22][23][24].
When notifying patients, provide written communication that explains:
- Details of the breach
- What PHI was involved
- Potential risks
- Steps to mitigate harm
- Contact information for further assistance [23]
For large-scale breaches (affecting 10,000 or more people), you’ll need to post a notice on your website and set up a toll-free hotline [23]. Be mindful of state-specific laws, which may require faster notifications - typically within 30 to 45 days. Submit your OCR report electronically via the HHS portal, including a four-factor risk analysis to confirm whether PHI was compromised [23][24].
Here’s a quick breakdown of reporting requirements:
| Breach Size | Individual Notification Timeline | HHS OCR Report Timeline | Media/Website Notice |
|---|---|---|---|
| <500 | Annual summary by 60 days post-year-end | Annual summary | No |
| 500-10,000 | 60 days from discovery | 60 days from discovery | Website/posting |
| >10,000 | 60 days from discovery | 60 days from discovery | Media + website |
Pre-drafted notification templates, available through HHS guidance, can help streamline communications during a breach [23]. After the incident is resolved, conduct a root cause analysis within 30 days, update your training materials, and share lessons learned with your board [10]. For organizations juggling multiple risks, platforms like Censinet RiskOps™ (https://censinet.com) can centralize breach documentation and help coordinate responses across teams. Regularly reviewing and updating your plan will strengthen your email security and prepare your organization for future challenges.
Conclusion
Protecting email communication under HIPAA regulations isn’t something you set up once and forget. It’s an ongoing effort that calls for regular updates, monitoring, and staff training. As Skirmantas Venckus and Anmol Ratan Sachdeva aptly state:
"HIPAA secure email compliance is not a one-time setup but an ongoing process that requires regular monitoring, updates, and staff training to ensure continued effectiveness and compliance" [1].
The stakes for non-compliance are high. Ensuring secure, HIPAA-compliant email involves key measures like encryption (TLS 1.2/1.3 and 256-bit standards), strict access controls (such as MFA and role-based permissions), and comprehensive audit logging [1][17]. These technical safeguards align with the secure email protocols discussed earlier. However, technology alone isn’t enough - staff must know how to handle PHI, apply encryption properly, and recognize potential security threats before they turn into breaches.
Automation tools, as highlighted in earlier sections, play a crucial role in reducing risks. Conducting regular audits - such as quarterly reviews of encryption success rates and access logs - can help uncover vulnerabilities and prevent risky shortcuts. Together, these efforts create a security framework that evolves over time.
It’s also critical to ensure that all third-party vendors sign a Business Associate Agreement (BAA) and that they offer HIPAA-compliant services [1][17]. This step is a cornerstone of the strategies for maintaining secure email practices.
For organizations managing multiple vendors or complex risk environments, platforms like Censinet RiskOps™ (https://censinet.com) can simplify compliance documentation and risk management. By treating email security as a continuous process - complete with regular training, updated protocols, and vigilant oversight - you’ll establish a strong defense that protects both your patients and your organization.
FAQs
Is TLS email encryption enough for HIPAA?
TLS encryption plays a key role in securing email communications and is considered an "addressable" safeguard under HIPAA regulations. However, relying on TLS alone may not fully satisfy HIPAA requirements. Meeting compliance standards requires a more comprehensive strategy that includes multiple layers of protection, such as encryption, proper key management, consistent monitoring, and additional measures like end-to-end encryption. Conducting regular risk assessments is also essential to pinpoint vulnerabilities and ensure adherence to HIPAA’s Security Rule.
What email details are considered PHI, including subject lines?
Email details classified as Protected Health Information (PHI) include email addresses and subject lines containing health-related information or personal identifiers. Examples of such identifiers are names, dates, or medical record numbers that could connect the information to a specific individual. These details require safeguarding to ensure compliance with HIPAA regulations.
How can we prevent staff from accidentally emailing PHI?
To reduce the risk of accidentally emailing PHI, it's crucial to implement end-to-end encryption protocols such as TLS 1.2 or 1.3. Pair this with secure email gateways that include data loss prevention (DLP) tools and enforce multi-factor authentication (MFA) for added protection. Regular HIPAA training for employees is equally important - educating staff about email security and proper PHI handling can significantly minimize human errors. By combining these technical measures with consistent awareness programs, you can strengthen compliance efforts and lower potential risks.


